In 2024, 9.5% of global M&A deals leaked; the highest rate recorded in 16 years of tracking by Intralinks. That means nearly 1 in 10 confidential transactions, with all of their financial models, IP portfolios, and strategic plans, found their way to the wrong people before a single signature hit the page.
The deals that leaked took an average of two additional weeks to close. Some didn't close at all.
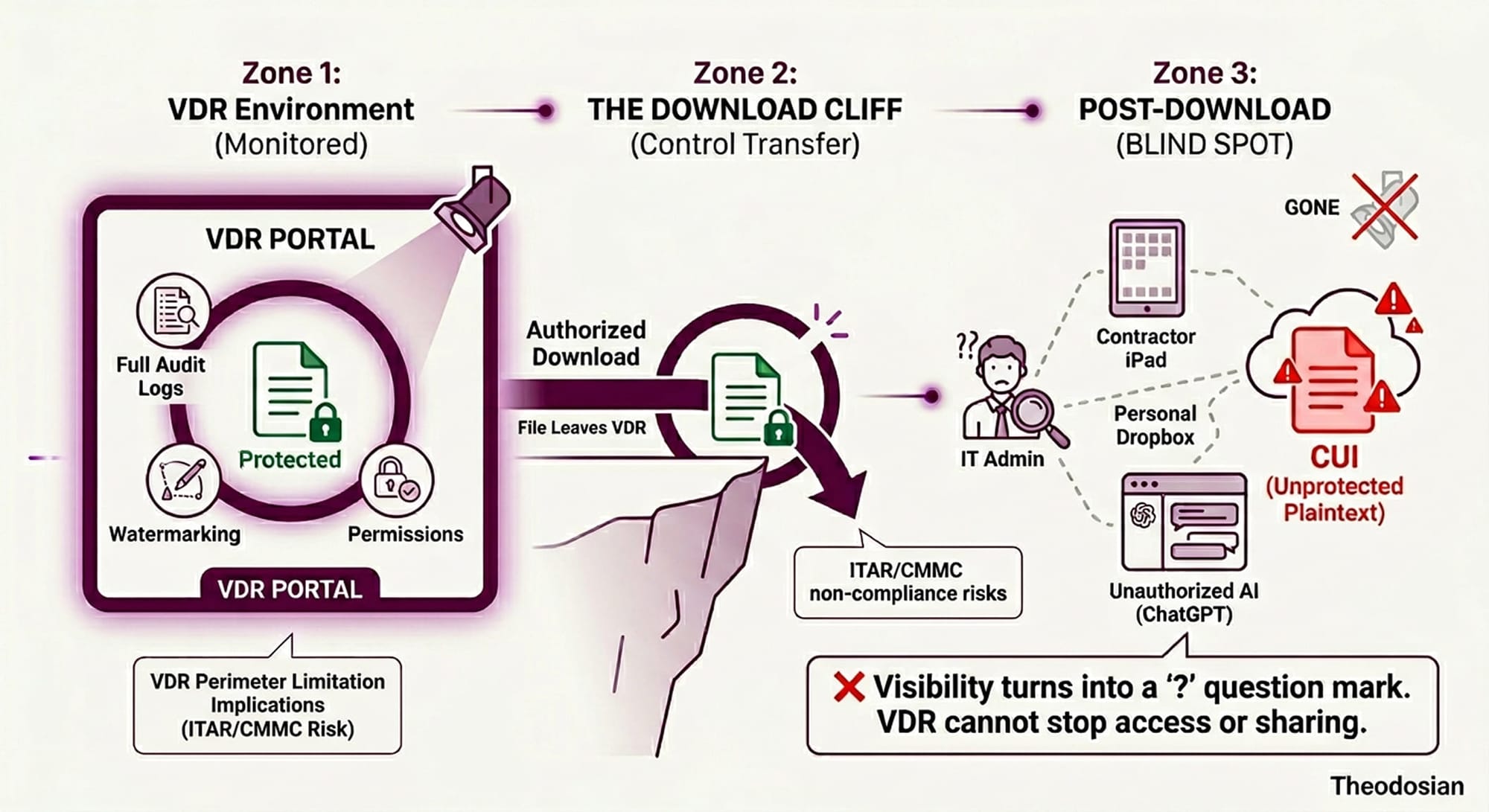
The security industry's response to this problem is the virtual data room. But here's what VDR vendors won't tell you in their product demos: a data room secures the room. Once a document walks out the door — downloaded by a legitimate user with compromised credentials, forwarded by a careless advisor, or exfiltrated by a disgruntled employee — the data room's security ends.
This is the gap that costs deals, triggers regulatory action, and ends careers.
What Does a Virtual Data Room Actually Do?
A VDR is, at its core, a secure file repository with access controls. The major platforms — Intralinks, Datasite, Firmex, and Ansarada — all offer variations on the same core toolkit: granular permissions, user activity logging, audit trails, document watermarking, and view-only modes that prevent printing or downloading.
These are legitimate security controls. They restrict who can see which documents, record who accessed what and when, and make it harder for a careless user to accidentally share a file. For managing the information hygiene of a due diligence process involving 200 advisors across four time zones, they're genuinely useful.
But every one of these controls is what security professionals call a detective or deterrent control. They catch or discourage bad behavior, but they don't prevent the data from being left in a dangerous state.
The moment a file is downloaded — and in almost every real deal process, some files are legitimately downloaded — the VDR has no further say in what happens to it. That file can be copied to a personal device, forwarded to someone not in the data room, uploaded to an insecure third-party service, or quietly exfiltrated by someone who has turned hostile.
The VDR knew who downloaded it. It logged the access event. But the file itself is now unprotected.
🔍 Check Your VDR Logs: Where Are Those Files Now?
A VDR audit log stops at the moment of download. If you can’t see what happened to your sensitive IP after it left the platform, your deal is at risk. See how we provide persistent visibility and control beyond the "Download Cliff."
The Post-Download Problem
Consider a realistic due diligence scenario. An investment bank's associate downloads a target company's manufacturing specifications to review offline during a flight. Their laptop is not encrypted at the file level. Their email client autocompletes to the wrong recipient. Or their device is taken in a targeted attack at their hotel.
The VDR audit log shows: File downloaded by [Associate Name], 2:47 PM, Tuesday. That's all anyone can do with that information.
This is not a hypothetical scenario either. The research is consistent: 52% of M&A deals uncover major cybersecurity risks during post-closing integration, after the price is locked in. By that point, the damage is already done. Sensitive IP, customer data, and trade secrets may have been circulating unprotected for months while the deal was live.
The underlying issue is that VDRs are perimeter tools. They build a secure perimeter around documents inside the platform. But regulated deals involve documents that exist in many places beyond the platform: legal memos on outside counsel's servers, technical drawings on engineering workstations, financial models in spreadsheets forwarded across teams. The data room never touches most of the sensitive material involved in a deal.
The Regulatory Exposure Is Real
This isn't just a business risk; it's a compliance problem with material consequences.
ITAR-controlled technical data in a defense or aerospace deal requires strict access controls that follow the document wherever it goes. The ITAR regulations (§ 120.31, § 120.33) govern who can access export-controlled technical information. A VDR grants access within its environment. It says nothing about what happens when that drawing is downloaded and emailed to an unvetted counterpart.
Material non-public information (MNPI) in any public company transaction is subject to SEC Rule 10b-5. A VDR tracks who accessed MNPI inside the room. It cannot prevent an authorized user from trading on that information outside it. If documents leave the VDR environment and end up in the wrong hands, the exposure is the same regardless of how the data room was configured.
Attorney-client privileged documents carry their own risk. Sharing privileged legal memos in a general-purpose data room — particularly with a broad range of advisors — can constitute an inadvertent waiver of privilege. Proper controls require keeping privileged materials either out of the VDR entirely or behind file-level access restrictions that follow the document after download.
The point is not that VDRs are negligent; they weren't designed to solve these problems. They were designed to manage access inside a controlled environment. The problem is when organizations treat "we have a data room" as equivalent to "our sensitive data is protected."
What IRM Does, and Why It's Not Enough on Its Own
Some VDR platforms offer optional IRM (Information Rights Management) as an add-on capability. IRM embeds encryption and access policy directly in the file, which means an authorized user must re-authenticate every time they open a document, and administrators can revoke access to downloaded copies.
This is closer to real protection. A revoked file is inaccessible even after download; the IRM policy travels with the document.
But IRM has deployment constraints that prevent it from covering the full problem. It requires client-side software or browser plug-ins on every device that opens a protected file. It typically covers a limited set of file formats. It adds friction to legitimate workflows that deal teams, under time pressure, will route around. And it still depends on the security posture of every endpoint that ever accessed the file.
More importantly, IRM is an optional add-on that most deal teams don't enable, and when they do, it's not applied uniformly across all sensitive documents.
The result is that a handful of files get IRM protection, while the financial models, term sheet drafts, and technical annexes circulate without it.
What Genuine File-Level Security Looks Like
The answer to the post-download problem is protection that doesn't end when the file leaves the platform. That means encryption and access controls that are embedded in the document itself, not in the repository around it.
Per-file FIPS 140-3 validated encryption means every document carries its own cryptographic key. Context-aware access controls govern whether the file can be opened based on the user's verified identity, device posture, location, and time — not just whether they were added to a data room user list weeks ago.
If the file is downloaded by an authorized user and later forwarded to someone who shouldn't have it, that person's attempt to open the file is an access request — and access is denied. Not a degraded experience. Not watermarked ciphertext. Denied.
If a device is compromised, access can be revoked at the file level — instantly, retroactively — regardless of where the file is stored. In a deal process with dozens of advisors across multiple organizations, that capability is the difference between a contained incident and a breach notification.
This model doesn't replace the data room. It closes the gap that every data room leaves open.
A Note on M&A Due Diligence Specifically
Due diligence creates unusual data security conditions that are worth calling out directly.
The sensitivity window is compressed. In a live deal, the most valuable documents — audited financials, IP portfolios, customer contracts, board presentations — are circulating widely for a defined period, after which the deal either closes or falls apart. The attacker who knows a deal is in progress has both a target and a deadline.
The user population is heterogeneous and temporary. Unlike your own employees, external advisors bring their own devices, their own security postures, and their own email clients. You have no visibility into — and no control over — how they handle the documents they've downloaded.
Disgruntled employees are a specific threat vector. In situations where a deal involves restructuring, layoffs, or integration, employees who expect to be displaced have both motive and access. Research cited by Verizon's 2025 DBIR noted a 100% increase in attacks involving third parties and supply chain partners — and deal processes are precisely the moment when an organization's document exposure to third parties is at its peak.
Building the right answer for this environment means starting with the assumption that files will leave your controlled environment. The security model has to account for that.
Five Questions to Ask Before Your Next Deal
Before the next due diligence process goes live, it's worth running through these questions with your security team:
- What happens to a downloaded file after it leaves the data room? If the answer is "we hope the advisor handles it responsibly," that's a gap.
- Do you have file-level encryption on your most sensitive documents, or just repository-level access controls? These are not the same thing.
- Can you revoke access to a specific document after it's been downloaded? If not, a compromised advisor becomes permanent exposure.
- Do your VDR security controls address the IRM gap, and are they applied uniformly, or just to some file types?
- If your most sensitive technical documents were exfiltrated from an advisor's device tomorrow, what would the regulatory notification obligation be? ITAR, MNPI, and privilege concerns don't wait for the breach to be convenient.
How Theodosian Addresses the Data Room Gap
Theodosian's per-file encryption and context-aware access controls address precisely the problem that VDRs leave open. Protection is embedded in each document, not in the platform around it. That means:
- Real-Time Contextual Denial: Access is denied automatically if security conditions—identity, device trust, or location—are not met. The system doesn't wait for a manual "revoke" command; it denies access.
- Persistent Enforcement: Files remain encrypted and policy-controlled regardless of where they travel after download (personal cloud, USB, or contractor devices).
- Strategic Revocation: While the system denies access by default for non-compliant contexts, administrators can manually revoke access for any specific user or file instantly, globally, and at any point in the deal lifecycle.
- Comprehensive Forensics: Every access attempt—whether granted, denied by context, or manually revoked—is logged with full identity and device metadata for audit purposes.
- Zero-Knowledge Architecture: Theodosian cannot access customer data, and neither can any third party, ensuring that "sovereignty over the keys" remains with the deal team.
For organizations handling ITAR-controlled technical data, MNPI, or attorney-client privileged documents in a deal context, this is the layer that ensures what leaves the data room is still protected.
Theodosian works alongside existing VDR platforms; it doesn't replace them. The data room manages access and workflow. Theodosian ensures the files themselves are self-defending.
📁 Secure Your Next Transaction With Per-File Encryption
See how Theodosian integrates with your existing VDR to provide persistent ITAR and MNPI protection.
FAQs: Virtual Data Room Security
What is the main security gap in virtual data rooms?
VDRs control access inside the platform — they log who accesses documents and can restrict viewing or downloading within the room. But once a file is legitimately downloaded by an authorized user, the VDR has no further control over it. The file can be copied, forwarded, or exfiltrated without any further protection. This is the core gap that per-file encryption addresses.
Does VDR watermarking prevent data leaks?
Watermarking is a deterrent and a forensic tool — it identifies the source of a leak after the fact, which is useful for internal investigations. It doesn't prevent a determined user from photographing a screen, using OCR to strip a watermark, or forwarding a downloaded file. It's a detective control, not a preventive one.
What happens to ITAR-controlled documents in a VDR?
ITAR regulations require that access to export-controlled technical data is limited to authorized persons, including after download. A VDR controls access within the platform. It cannot enforce ITAR access restrictions on a file once it has been downloaded to an advisor's laptop and forwarded via email. Organizations sharing ITAR-controlled data in a deal context need file-level access controls that travel with the document.
What is the difference between IRM and VDR access controls?
VDR access controls are repository-level: they determine who can log into the data room and what they can see. IRM (Information Rights Management) embeds encryption and access policy in the file itself, which means the policy travels with the document after download. IRM is more protective but requires client-side software on every endpoint and isn't supported for all file types. Most VDRs offer IRM as an optional add-on, not a default.
What should you do if sensitive documents are downloaded from a VDR by an unauthorized person?
With standard VDR controls, your options after an unauthorized download are limited to reactive forensics: audit log reviews, watermark tracing, and legal action.
With Theodosian’s file-level protection, the file itself enforces your security policy. If the person is unauthorized—or if an authorized person tries to open the file from an unmanaged device or restricted location—access is denied automatically. The file simply will not decrypt because the contextual requirements (identity, device trust, location) are not met.
Furthermore, if an authorized user’s access needs to be terminated—such as a contractor roll-off or a detected credential compromise—you can revoke access globally in seconds. The file becomes a useless encrypted block even on the device it was originally downloaded to.
How does data room security affect M&A deal risk?
According to Intralinks' 2024 M&A Deal Leaks Report, 9.5% of global deals leaked in 2024 — the highest rate in 16 years. Leaked deals took an average of two additional weeks to close, and some collapsed entirely. Separately, 53% of M&A professionals consider undisclosed data breaches an immediate deal-breaker, and 52% discover major cybersecurity issues during post-closing integration. Strong data security during a deal process protects not just the documents but the deal itself.
