Shadow data isn't created by bad actors. It's created by your authorized users, following normal business processes, using approved tools. Every time a loan file is sent to an auditor or a design spec is shared with a subcontractor, a legitimate transfer occurs—and every one of them creates a file that now lives outside your security perimeter, with no ongoing governance attached to it.
The scale of this exposure is staggering. Wiz 2025 Cloud Data Security Snapshot, 54% of cloud environments currently harbor sensitive data in these unmanaged shadow stores. Even more critical for organizations relying on structured data, 72% of cloud environments contain publicly exposed PaaS databases operating without sufficient access controls. When these structural failures intersect with sensitive data, traditional perimeter-based tools fail because they cannot govern the data itself once a "legitimate" boundary is crossed.
The attack surface isn't just your servers. It's every file that was legitimately shared and then abandoned by tools that stop at the boundary.
🛡️ Quantify Your Shadow Data Exposure
See how file-centric governance protects your IP, even on contractor endpoints and personal cloud accounts.
The Five Shadow Data Vectors
Shadow data accumulates through five predictable vectors. None of these vectors require a policy violation to create exposure.
SaaS Platform Exports
Business users export reports, records, and customer data from Salesforce, ServiceNow, Workday, and similar platforms to Excel files for analysis. These exports contain the same sensitive data as the source system, but without the source system's access controls. The exported file travels to a laptop, gets emailed, gets saved to a shared drive; each step creates a new uncontrolled copy with no expiry, no revocation capability, and no audit trail.
Email Attachments with No Expiry
Contracts, financial statements, HR documents, and technical specifications sent via email arrive at the recipient's inbox and stay there indefinitely. The sender has no ability to revoke access, no visibility into whether the file was forwarded, and no record of subsequent access. For organizations subject to ITAR or CMMC, email attachments containing controlled technical data are a compliance liability that compounds every time the file changes hands.
Collaboration Platform Residue
Microsoft Teams channels, Slack workspaces, and SharePoint sites accumulate files over project lifecycles. When a project closes, and guest access is revoked from the collaboration platform, the files shared during the project frequently remain in guest users' download histories, exported archives, and personal cloud storage. Platform-level access revocation does not revoke access to files already downloaded.
Contractor Endpoint Retention
Contractors with authorized project access routinely retain files on personal laptops after project closure. For CMMC-scoped organizations, this is among the most common assessment findings in 2025–2026: CUI present on endpoints outside the system security plan boundary, on devices outside managed device policy, with no technical controls enforcing access expiry. The contractor's VPN access was revoked, but the file was not.
Personal Cloud Sync
Employees using iCloud, Google Drive, or Dropbox personal accounts, even casually, for convenience, may sync work files to personal cloud storage without intent to exfiltrate data. The result is organizationally sensitive files in a personal cloud environment with no corporate governance, no visibility, and no revocation capability.
The Hidden Pipeline: Learn how unauthorized LLM usage creates an invisible data leak in our Governance Guide to Shadow AI.
The Agentic Gap: Discover why autonomous agents require a file-resident security architecture in our Technical Analysis of Agentic AI Security.
Why Classification Alone Doesn't Close the Gap
Data classification tools identify what data is sensitive. A discovery tools catalog is where sensitive data resides on monitored systems. Neither capability governs the data after it leaves those systems. Classification without persistent policy enforcement is labeling without control.
The gap: a file classified as CUI at the point of creation has a classification tag on the originating system. When it is emailed to a subcontractor, downloaded to a contractor's laptop, or exported to a personal cloud sync folder, the classification tag doesn't travel with persistent enforcement. The file is identifiable as sensitive, but that identification provides no governance over who accesses it, from where, or for how long.
This "enforcement blind spot" exists because most security stacks rely on point-of-transfer rules rather than file-level architecture. For a deep dive into why these traditional boundaries fail, read Data Access Governance: Why DLP Fails at the File Boundary.
To close this gap and move beyond simple labeling, your security architecture must incorporate three specific technical capabilities:
- Classification Must Bind Policy: Instead of just applying a label, classification should attach an access policy that travels with the file, independently of the network or the originating system.
- Protection Must Be Persistent: Encryption applied at the point of creation must remain in effect regardless of how many copies are made or where they travel.
- Revocation Must Be Retroactive: When a project closes, a partnership ends, or access is terminated, every copy of every governed file must reflect the revocation at the next access attempt, not just the copy on the originating server.
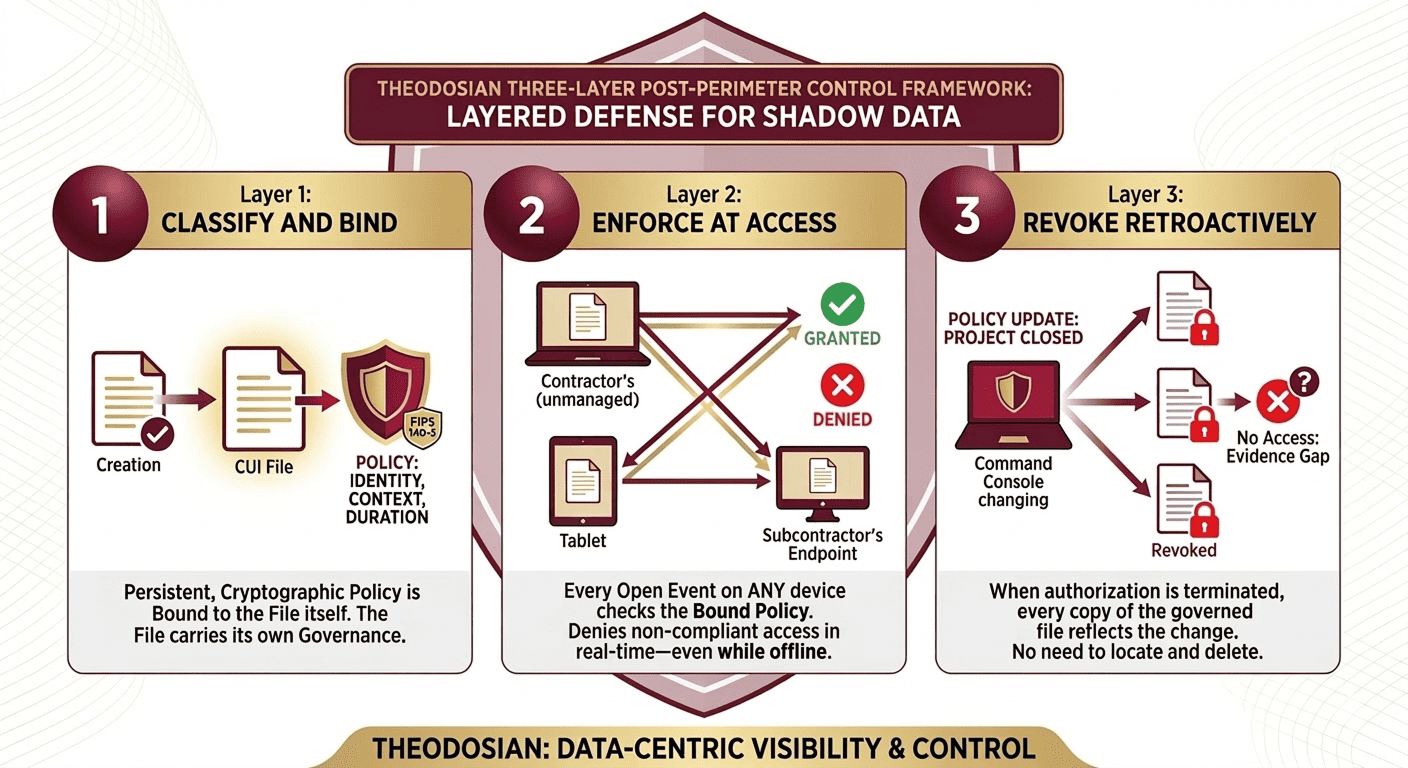
The Three-Layer Post-Perimeter Control Framework
Governing shadow data requires controls that operate outside the perimeter. To maintain compliance where your visibility ends, follow this three-layer framework:
Layer 1: Classify and Bind
At the point of creation or first authorized transfer, apply a file-level policy that defines who can access the file, under what conditions, and for how long. This is not a DLP rule; it’s a persistent, cryptographic access policy bound to the file itself. The file carries its own governance.
Layer 2: Enforce at Access
Every time the file is opened, on any device, in any location, the access policy is checked. Is the accessing identity still authorized? Is the device compliant? Is the access occurring within the permitted time window or geographic scope? If any condition fails, access is denied. This check works offline; it does not require connectivity to the originating system.
Layer 3: Revoke Retroactively
When the access policy changes, because a project ends, a partnership dissolves, or a user's authorization is terminated, every copy of the file reflects the change at the next access. There is no need to locate and delete all copies. The file becomes inaccessible to unauthorized users regardless of where it resides.
Compliance Implications Across Regulated Verticals
Shadow data exposure creates specific compliance liability in regulated environments:
ITAR and EAR: Uncontrolled technical data on contractor endpoints, in personal cloud storage, or in email archives accessible outside the United States constitutes a potential export control violation, regardless of how the original transfer occurred. ITAR does not make exceptions for authorized transfers that subsequently become uncontrolled. The obligation to control technical data persists after transfer.
CMMC Level 2: NIST SP 800-171 control 3.1.3 requires limiting the flow of CUI to authorized users and systems. A contractor retaining CUI on a personal device outside the system security plan boundary is a direct violation of 3.1.3, and among the most common findings in current CMMC assessments. The enforcement is against the originating organization, not the contractor.
GDPR and International Data Protection: GDPR Article 17 (right to erasure) requires organizations to delete personal data on request. When personal data has proliferated into shadow data stores, contractor laptops, email archives, and personal cloud accounts, compliance with Article 17 deletion requests becomes technically impossible without per-file revocation capability.
Identifying Shadow Data Exposure in Your Environment
Assessing shadow data exposure requires answering four questions that standard DLP reporting cannot answer:
- For every sensitive file that left your organization in the last 12 months, where does it currently reside?
- Who has accessed those files since the original transfer, and from which devices and locations?
- Which files are currently accessible to users whose authorization has since been revoked?
- Which files reside on contractor or partner endpoints outside your security boundary?
If these questions cannot be answered from your current security tooling, you have an unquantified shadow data exposure. The 54% exposure figure is not a freak outcome; it is the predictable result of authorized file transfers with no post-transfer governance.
Start Quantifying Your Shadow Data Exposure
The files you know about are governed. The files you don't know about are the ones that appear in breach reports. Shadow data exposure is not an edge case; it's a predictable byproduct of normal file sharing, and it accumulates with every authorized transfer that has no post-transfer governance attached.
Theodosian's data access governance approach binds policy to the file at creation or first transfer, so every copy, on every device, in every location, remains governed. Theodosian's per-file encryption approach is patent-pending. Access is revocable retroactively. Every access event is logged with a cryptographic timestamp. The file defends itself.
🤖 Secure Your Data Beyond the Perimeter
Transition to a data-centric architecture with Theodosian. In just 14 days, we can show you how to embed FIPS 140-3 validated encryption and persistent audit trails directly into your files.
FAQs: Shadow Data and DLP
What is shadow data, and how is it different from shadow IT?
Shadow IT refers to unauthorized applications, services, or infrastructure used without IT approval. Shadow data refers to sensitive files that have left organizational control through authorized channels, legitimate file transfers, email attachments, contractor downloads, SaaS exports, and now reside in locations with no ongoing governance. Shadow data does not require unauthorized tools to create. It is a byproduct of normal business operations: every file shared with a partner, auditor, or contractor that carries no post-transfer governance becomes shadow data.
Why can't DLP tools find and govern shadow data?
DLP tools enforce policy at transfer points, email gateways, cloud upload boundaries, and USB ports. Once a file has been legitimately transferred (which DLP permitted), DLP has no ongoing authority over that file. DLP cannot access partner systems, contractor endpoints, or personal cloud storage to audit or govern files that reside there. Discovery tools can catalog sensitive data on monitored internal systems, but they have no jurisdiction over files that leave those systems through authorized channels.
How does per-file encryption address shadow data governance?
Per-file encryption binds the access policy to the file cryptographically. The file carries its own governance, independently of whether it resides on a corporate server, a partner's system, a contractor's laptop, or a personal cloud storage account. When the file is opened, the cryptographic access check evaluates whether the accessing identity is currently authorized under the file's policy. If authorization has been revoked, access is denied, regardless of location. This is distinct from server-side encryption, which only protects data on the server itself and provides no governance after legitimate download.
What is the CMMC compliance implication of contractor endpoint shadow data?
NIST SP 800-171 control 3.1.3 requires organizational systems to control the flow of CUI to authorized users and authorized systems. When CUI resides on a contractor's personal device — even after legitimate project access — it is outside the system security plan boundary and outside the organization's managed device policy. This is a direct gap under 3.1.3 and is among the most commonly cited findings in current CMMC Level 2 pre-assessments. The originating organization bears compliance responsibility for CUI it shared, not just CUI on its own systems.
How does shadow data exposure relate to ITAR and export control compliance?
ITAR (22 CFR §§ 120–130) and EAR (15 CFR §§ 730–774) require ongoing control over export-controlled technical data. The obligation does not end when data is legitimately transferred to an authorized domestic recipient. If controlled technical data subsequently migrates to an unauthorized location (personal cloud storage accessible outside the US, a contractor's personal device, a foreign national's system), this creates potential export control exposure regardless of how the original transfer occurred. Organizations must maintain the ability to govern and revoke access to controlled technical data after authorized transfer, not just at the point of initial sharing.
