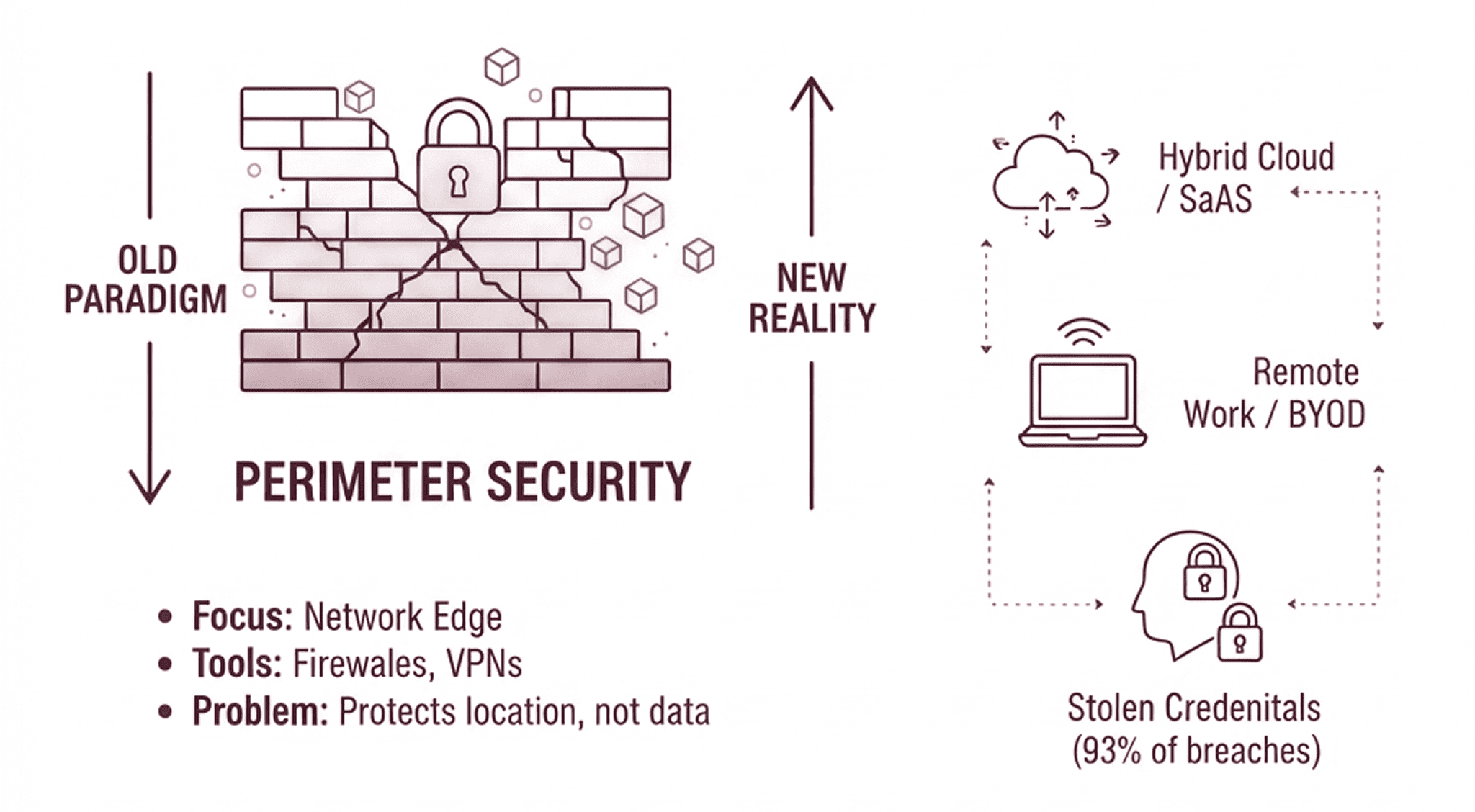
Let’s be blunt: For decades, there have been platforms and software that build bigger, stronger, more expensive walls around our data. Firewalls, VPNs, proxies, intrusion detection systems—a dizzying array of perimeter defenses designed to keep the bad people out. Yet, here we stand in 2026, and the data breach headlines are worse than ever.
The average cost of a data breach has soared to an estimated $4.45 million globally in 2023, with recent estimates for U.S. organizations surging to a record $10.22 million in 2025/2026.
Despite global spending on information security projected to reach $248 billion in 2026, the frequency of cyberattacks has more than doubled since 2020, with high-growth sectors seeing a 40% increase in successful exfiltrations during the same period.
The entire paradigm of "keeping threats out" is obsolete in a world where inside is the new outside. Your multi-million-dollar perimeter is failing, and it’s time to understand why.
🛡️ Is Your CUI Truly Protected After the Download?
Don’t let a single "Save As" click jeopardize your CMMC 2.0 or ITAR standing. Discover how Theodosian keeps your sensitive data compliant even when it leaves your secure cloud tenant.
The Myth of the Unbreachable Wall: How Perimeter Security Died
Imagine guarding a priceless vault. You build thick walls, laser grids, and biometric scanners. Impenetrable, right? But what if the guard you hired walked in through the front door and then just handed over the blueprints?
This isn’t hypothetical in 2026:
- The Rise of Identity-Based Attacks:
- 93% of breaches involve stolen credentials.
- This means your firewall lets them in. Your VPN authenticated them. Your fancy IDP system gave them a pass. The threat isn't outside the wall; it walked through the front gate.
- The Remote Work & Hybrid Cloud Exodus:
- The "network perimeter" dissolved years ago. Your data lives everywhere: SaaS apps, personal devices, contractor laptops, multi-cloud environments.
- Trying to "fence off" these distributed endpoints with traditional network tools is like trying to catch water with a sieve. The data simply flows around it.
- The Download Dilemma: CMMC, ITAR, & Regulatory Catastrophe:
- Think your data is safe in Microsoft 365 GCC High or Google Workspace Enterprise? It is, until someone downloads it.
- The moment a Controlled Unclassified Information (CUI) file leaves that compliant tenant and lands on a local hard drive, an email, or a USB stick, your regulatory compliance (CMMC, ITAR, HIPAA, GDPR) vanishes. That secure tenant just became a high-speed data delivery service for non-compliant data.
- The Problem: Your network security has no control over a file once it's downloaded. Zero. None.
Stop Protecting the Pipes, Start Protecting the Water
The buzzword 'Zero Trust' is everywhere, but most implementations stop at the front door. They verify the user and the device to let them into the network.
At Theodosian, we believe verification shouldn't end at the login screen. We apply ‘Verify every user, every device, every time’ directly to the file itself. This means even a 'verified' user on a 'verified' device cannot access a document unless every layer of your specific data-level policy is met.
Operators can choose from an array of granular enforcement settings—restricting access by geographic location (geofencing), specific IP ranges, time-of-day windows, and even the specific application being used to open the file. We don't just secure the access; we secure the asset by ensuring it only exists in the exact context you authorize.
The Paradigm Shift: Data-Centric Security
Instead of building a fortress around the office, what if every single sensitive document, every blueprint, every client list, every piece of CUI was inherently secure, no matter where it went?
This is data-centric security – encrypting the data itself, not just the network it travels on.
- File-Level Encryption: Every sensitive file is encrypted at its core. If it’s downloaded, emailed, or transferred, it remains encrypted and protected.
- Dynamic Access Control: Access isn't just "yes" or "no." It's "yes, but only for 24 hours," or "yes, but only from a specific device," or "yes, but read-only." You control the data, not just the network.
- Context-Aware Protection: If a file is accessed from an unapproved location, or by a user with unusual behavior, access can be revoked instantly – even after the file has left your environment.
The "Oh S***!" Moment for CMMC 2.0 & ITAR Compliance
This isn't just about general security; it's about survival for defense contractors and any organization handling sensitive data.
CMMC 2.0 (now live with mandatory SPRS submissions and looming 3rd party audits) and ITAR (International Traffic in Arms Regulations) compliance doesn't care if your Google Drive is secure. It cares if the data itself is protected, even when it’s offline or outside your primary cloud tenant.
If an unencrypted CUI file is downloaded onto an engineer's laptop, and that laptop gets stolen, you are in breach. Full stop. No firewall in the world could have prevented that. Only encryption at the file level saves you.
Your Next Steps for Real Security in 2026
The physics of the network have shifted: there is no longer an 'inside' to protect. Your defenses must evolve to reflect that reality. Stop throwing money at perimeter solutions that are demonstrably failing.
It’s time to ask:
- Where does my most sensitive data actually live and travel?
- How do I protect that data when it leaves my primary control?
- Am I truly compliant with CMMC/ITAR, or just hoping my perimeter holds?
The era of the firewall as your primary defense is over. It's time to put the security directly on the data itself.
🚀 Stop Defending the Perimeter. Start Defending the Data!
The $10 million breach is the new normal, but it doesn't have to be yours. See how Theodosian’s file-level encryption makes exfiltrated data useless to attackers and insiders alike.
FAQs: Perimeter Security vs. Data-Centric Security
What is perimeter security, and why is it failing in 2026?
Perimeter security refers to defending the boundary of a network, like firewalls protecting an office network. It's failing because modern work is distributed (remote, cloud), and most breaches now originate from compromised internal credentials, allowing attackers to bypass the perimeter.
How do CMMC 2.0 and ITAR relate to data-centric security?
CMMC 2.0 and ITAR require stringent protection for Controlled Unclassified Information (CUI) and sensitive technical data. Traditional perimeter security often fails to protect this data once it's downloaded or shared outside a compliant environment. Data-Centric Security (DCS) ensures CUI remains encrypted and controlled even after it leaves your network, which is critical for meeting these regulatory requirements.
Is my Microsoft 365 or Google Workspace compliant enough for CMMC/ITAR?
While cloud platforms like M365 GCC High or Google Workspace Enterprise offer compliance frameworks, they primarily secure data within their tenancy. The moment a CUI file is downloaded, emailed, or transferred outside that secure environment, it loses that protection and becomes non-compliant. Data-Centric Security (DCS) is needed for persistent protection.
What are the biggest risks of relying solely on perimeter security today?
The biggest risks include insider threats (malicious or accidental), credential theft, advanced persistent threats (APTs) that bypass firewalls, the proliferation of data across unmanaged devices, and severe non-compliance penalties from regulations like CMMC, ITAR, HIPAA, and GDPR once data leaves the perimeter.
