If you're reading this, you're probably not idly curious.
Maybe you have an audit coming. Maybe a gap analysis surfaced something you weren't expecting. Maybe someone on your team raised a flag that's now being escalated. Whatever the trigger, the question is real: what actually happens if ITAR or CMMC non-compliance is found?
The answer depends on several factors — who finds it, when, how serious it is, and what you do next. This post covers each of those variables honestly, including the parts that are genuinely serious and the parts where the outcome is within your control.
ITAR Violations: What the Penalties Actually Are
ITAR is enforced by the Directorate of Defense Trade Controls (DDTC) at the State Department. The penalties exist on two tracks — civil and criminal — and the distinction matters significantly.
Civil penalties can reach $1,271,078 per violation, or twice the value of the transaction involved, whichever is greater. For an organization with multiple violation instances — every unauthorized disclosure of a controlled document is a separate violation — these numbers compound fast.
Criminal penalties apply to knowing and willful violations: up to $1 million per violation and up to 20 years in prison per count. Criminal prosecution is reserved for deliberate or egregious conduct, but the threshold for "willful" is not as high as it sounds. Failing to implement compliance controls after being on notice of the requirement can satisfy a willfulness standard.
Debarment follows a criminal conviction automatically. A felony conviction for an ITAR violation results in mandatory debarment from exporting, manufacturing, or furnishing any defense article or service — effectively ending a defense contractor's business model. Debarment typically runs three years.
The 2024 Raytheon settlement — exceeding $950 million for ITAR and Arms Export Control Act violations, including contract cost inflation and misrepresentations in export license filings — illustrates what enforcement at the large contractor level looks like. Earlier examples include 3D Systems Corporation ($20 million for unauthorized exports to Germany, China, and Taiwan) and a March 2023 settlement reaching $27 million for unauthorized exports.
These aren't outliers. The DDTC's enforcement posture has been consistently active, and enforcement actions have accelerated as defense supply chain scrutiny has increased.
Is Your Audit Trail Ready for a DDTC Review?
Penalties are determined by "good faith." The fastest way to prove it is with an immutable, file-level audit trail that shows exactly who accessed your data, and who was denied.
The Voluntary Disclosure Option and Its Limits
ITAR has a voluntary disclosure process under 22 CFR § 127.12. If your organization discovers a potential violation before the government does, proactively disclosing to DDTC is a significant mitigating factor in how the violation is handled.
The process has hard requirements. Initial notification must go to DDTC immediately upon discovery. Full disclosure — documenting the scope of the violation, all affected transactions, and what happened — must follow within 60 calendar days. If you miss that window, or if your initial disclosure is incomplete, the voluntary disclosure treatment is forfeited.
What voluntary disclosure can do: DDTC has discretion to treat the disclosure as a mitigating factor, reduce administrative penalties, and exercise restraint on whether to pursue criminal referral to the DOJ. Whether disclosure results in no penalty, reduced penalty, or full penalty depends on the nature and scope of the violation, whether it would have been authorized under a proper license, and evidence of good-faith remediation.
What voluntary disclosure cannot do: eliminate liability. You are still disclosing a violation. The outcome depends on what you disclose and what you do next. Voluntary disclosure doesn't prevent penalties — it creates an opportunity to influence them.
One critical caveat: if the DDTC or any other US government agency is already aware of the violation when you disclose, your disclosure is no longer voluntary in the eyes of the regulation, and the mitigation treatment is gone.
CMMC Non-Compliance: The Enforcement Process
CMMC enforcement operates through a different mechanism than ITAR, and understanding the sequence matters for how you respond.
Phase 2 begins November 10, 2026: From that date, new solicitations for contracts involving Controlled Unclassified Information will require C3PAO third-party assessments. Contractors without certification cannot bid on affected contracts.
How violations are discovered: There are two main paths. First, a C3PAO assessment finds gaps during the certification process. Second, a cyber incident triggers mandatory reporting under DFARS 252.204-7012 — any incident affecting a Covered Contractor Information System (CCIS) that processes, stores, or transmits CUI must be reported to the DoD Cyber Crimes Center (DC3) within 72 hours of discovery. That report starts a clock and brings DoD visibility into your security posture.
What happens after a C3PAO assessment finding? If gaps are identified during assessment, the assessor provides findings to the contractor and to the DoD. The contractor has up to 180 days of conditional certification — provided all identified gaps are documented in a Plan of Action and Milestones (POA&M) — to remediate and close those gaps. The 180-day window is hard. If POA&M items aren't fully closed within that period, conditional certification expires, and the contractor is no longer eligible for new DoD contracts requiring CMMC.
Critical limitation on POA&M eligibility: only 1-point CMMC controls can be deferred to a POA&M. Controls weighted at 3 or 5 points — which include encryption requirements (SC.3.177), key management (SC.3.187), and media protection (MP.2.121) — must be fully implemented before a certification can be granted at all.
What happens when DoD discovers non-compliance outside the assessment process? Standard contract remedies apply: cure notices, termination for convenience, termination for default, and negative past performance ratings that follow the contractor into future bids. For serious cases, suspension and debarment proceedings.
The SPRS Score and What It Exposes
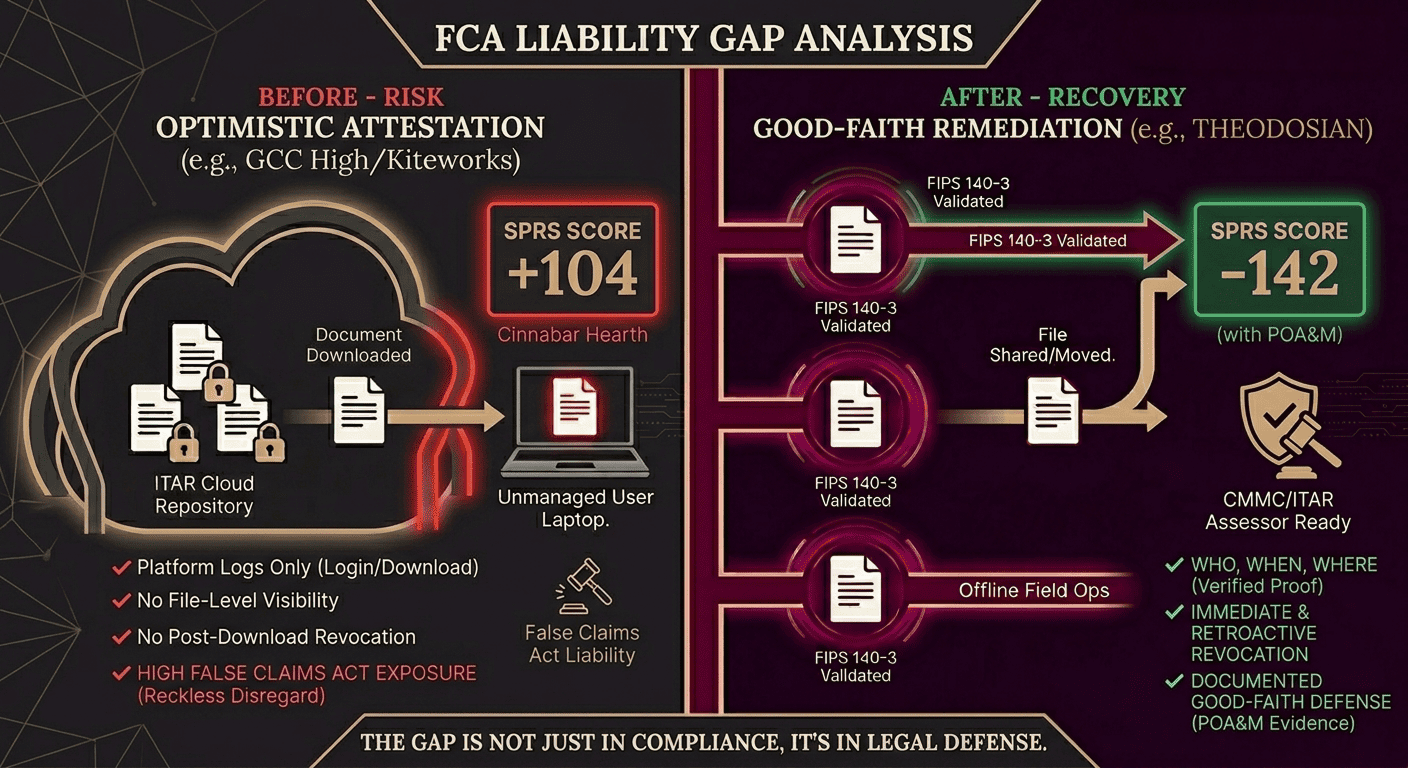
Every DoD contractor is required to submit a SPRS (Supplier Performance Risk System) score reflecting their NIST SP 800-171 compliance status. The score runs from -203 to +110. An honest score for a typical contractor that hasn't fully addressed the 110 NIST controls often lands negatively.
The problem is that many contractors submitted optimistic SPRS scores — and the False Claims Act now creates serious liability for those submissions.
The MORSE Corp case: In 2025, MORSE Corp settled a False Claims Act complaint for $4.6 million. The allegation: they had submitted a SPRS score of 104 while their actual assessed score was -142, a 246-point gap. The basis for FCA liability was the annual compliance affirmation they signed as part of DoD contract submissions, certifying compliance that didn't exist.
The Health Net Federal Services case: HNFS settled for $11.25 million in 2025 for cybersecurity violations spanning 2015–2018 — falsely certifying TRICARE contract compliance for years while audit findings documented the gaps internally. The "reckless disregard" standard under the False Claims Act doesn't require intent to deceive. Signing annual compliance affirmations without verifying their accuracy — particularly when internal audits have flagged gaps — satisfies the legal threshold.
The current exposure: The CMMC rule requires annual affirmations of compliance status throughout a contract's life. FY2025 saw $52 million recovered across nine cybersecurity-related FCA cases. DOJ has explicitly signaled that cybersecurity compliance fraud is a priority enforcement area.
For any contractor whose SPRS score doesn't reflect reality, the annual affirmation cycle is the mechanism through which FCA liability accrues. Every affirmation is a representation to the federal government.
What Good-Faith Remediation Actually Looks Like
Both ITAR and CMMC enforcement give credit for good-faith remediation — but the evidence has to be real, contemporaneous, and specific.
A POA&M is the foundation, not the ceiling. For CMMC, a POA&M documents identified gaps, remediation activities, resource commitments, and milestone dates. An approved POA&M is required for conditional certification. But a POA&M that sits in a document without evidence of active progress doesn't demonstrate good faith to an assessor, a contracting officer, or a DOJ attorney.
What enforcers look for:
- Self-identification: Did you find the gap, or did the government?
- Timeline: How long did you know about it before acting?
- Resource allocation: Budget line items, personnel assignments, tool procurement — documented before the enforcement conversation
- Third-party verification: Engagement with a C3PAO, a qualified assessor, or an independent consultant to validate remediation progress
- Executive accountability: Board or C-suite sign-off on the remediation plan and its milestones
- Evidence of improved controls: Configuration documentation, audit logs, training records — all generated during remediation, not reconstructed after discovery
This matters. A contractor who identifies a gap, documents it in a POA&M, allocates budget, and closes it within 180 days with documented evidence is in a fundamentally different position than one who ignores a known gap and affirmatively certifies compliance.
The Audit Trail as Both Risk and Defense
The same audit logging that exposes a violation is also the primary tool for demonstrating remediation. This is where the architecture of your security controls matters as much as the controls themselves.
Per-file access logging — records of every open, view, download, and denied access attempt at the file level — provides the kind of evidence that CMMC assessors, DDTC reviewers, and DOJ attorneys can evaluate. It answers the questions that matter in enforcement: who had access to this CUI, when, from where, and was any access attempt denied?
An audit trail that only records platform-level events (logins, uploads) without file-level access events doesn't demonstrate the granular CUI tracking that SC.L2-3.13.10 and AU.2.041 require. It also doesn't support the "good faith remediation" narrative in an enforcement context — because you can't show you were protecting the data if you have no evidence of how it was accessed.
For contractors currently without file-level audit logging, this is one of the highest-priority gaps to close — both for assessment readiness and for any enforcement scenario where demonstrating good faith requires evidence, not assertions.
A Practical Response Checklist
If you're reading this because something has already surfaced, here is a practical sequence:
✔️ Stop the active exposure: If there is an ongoing disclosure or unauthorized access, address it immediately. The length of time a violation continues is a factor in penalty severity.
✔️ Preserve everything: Don't delete logs, emails, or access records. Under DFARS 252.204-7012, you're required to preserve affected system images and logs for 90 days minimum following a cyber incident.
✔️ Engage legal counsel before disclosing: Whether the path forward is ITAR voluntary disclosure or CMMC POA&M, legal counsel should be involved before any formal disclosure to the government.
✔️ Conduct your own scope assessment: Don't rely on the government's scope — understand exactly which files, systems, and transactions are involved before your disclosure is complete.
✔️ Document remediation activities from day one: Everything you do to fix the gap should be documented as you do it, not reconstructed later. Dates, responsible parties, decisions made, resources allocated.
✔️ Assess your SPRS score honestly: If your submitted score doesn't reflect your current posture, the window to address this proactively — before an assessment or enforcement action — is now.
✔️ Get a gap assessment: An independent third party can tell you where you stand and give you a defensible baseline for remediation planning.
Stop Guessing at Your SPRS Score
FCA liability lives in the gap between what you say you do and what you can prove. Close your encryption and audit gaps in 14 days with our CMMC-ready pilot.
FAQs: ITAR and CMMC Non-Compliance
What is the maximum ITAR penalty per violation?
The current civil penalty for an ITAR violation is $1,271,078 per violation, or twice the value of the transaction, whichever is greater (per the Federal Register 2024 Civil Monetary Penalties Adjustment). Criminal penalties for knowing and willful violations reach $1 million per count and up to 20 years in prison. Each unauthorized disclosure of controlled technical data is a separate violation — for an organization with multiple files shared outside authorized channels, the aggregate exposure grows accordingly.
What is the difference between ITAR voluntary disclosure and a discovered violation?
Voluntary disclosure under 22 CFR § 127.12 gives the DDTC discretion to treat the disclosure as a mitigating factor — potentially reducing administrative penalties and limiting criminal referral. A discovered violation (where the government finds it first) carries no such discretion. Full penalties apply. Voluntary disclosure requires immediate initial notification to DDTC and a complete written disclosure within 60 days. If DDTC is already aware of the violation, the voluntary nature of the disclosure is forfeited.
What is a CMMC POA&M, and how does it affect contract eligibility?
A Plan of Action and Milestones document identified CMMC compliance gaps, remediation steps, responsible parties, resources, and milestone dates. An approved POA&M is required for conditional CMMC certification. Conditional certification allows contract performance for up to 180 days while gaps are remediated. If all POA&M items are not fully closed within 180 days, conditional certification expires, and the contractor becomes ineligible for new awards requiring CMMC. Only 1-point controls can be deferred to a POA&M — 3, and 5-point controls must be implemented before any certification is granted.
What is the False Claims Act exposure for CMMC non-compliance?
The False Claims Act (31 U.S.C § 3729) imposes liability — treble damages plus $11,665–$23,330 per false claim — on contractors who make false representations to the federal government, including the "reckless disregard" standard. CMMC requires annual compliance affirmations throughout a contract's life. A contractor who signs those affirmations while knowingly failing CMMC controls — or who fails to verify the accuracy of affirmations despite internal audit findings — creates ongoing FCA liability. The MORSE Corp ($4.6M) and Health Net Federal Services ($11.25M) settlements illustrate the financial exposure. DOJ recovered $52M+ in FY2025 cybersecurity FCA cases and has explicitly prioritized this area.
What triggers mandatory DFARS 252.204-7012 cyber incident reporting?
Under DFARS 252.204-7012, any cyber incident affecting a Covered Contractor Information System (CCIS) that processes, stores, or transmits Covered Defense Information (CDI) must be reported to the DoD Cyber Crimes Center (DC3) within 72 hours of discovery. This includes breaches, unauthorized access, and compromise of CUI — regardless of whether an encryption attack, exfiltration-only, or other mechanisms were involved. Reporting obligations also include preserving system images and logs, submitting malicious code samples to DoD, and retaining all incident data for 90 days.
What evidence does DoD or DDTC look for in a good-faith remediation defense?
Enforcers look for contemporaneous evidence (created during remediation, not after enforcement begins), specific (identifies the gap, the fix, the timeline, and who is responsible), and documented through objective records rather than assertions. Key elements: a POA&M with specific milestones and resource allocation; evidence of self-identification before government discovery; engagement of third-party assessors or C3PAOs to validate progress; executive-level accountability and sign-off; and audit logs demonstrating improved controls are operational. The earlier remediation begins, the more credible the good-faith narrative.
