Your backup strategy works. You can restore from an immutable copy in under four hours. You tested it. You have the runbook. And a growing percentage of ransomware gangs don't care.
The shift is documented, and the numbers are striking. According to Arctic Wolf's 2025 Threat Report, exfiltration-only ransomware attacks — where attackers steal data and demand payment to suppress its publication, without ever encrypting a single file — jumped from 2% to 22% of incident response cases in a single year. That's an 11x increase. Meanwhile, Mandiant's M-Trends 2025 report found that 77% of ransomware intrusions in 2025 involved confirmed data theft, up from 57% the year before.
The operational takeaway is uncomfortable: the backup problem is solved. The data problem isn't.
The Evolution of Cyber Extortion: From System Encryption to Data Exfiltration
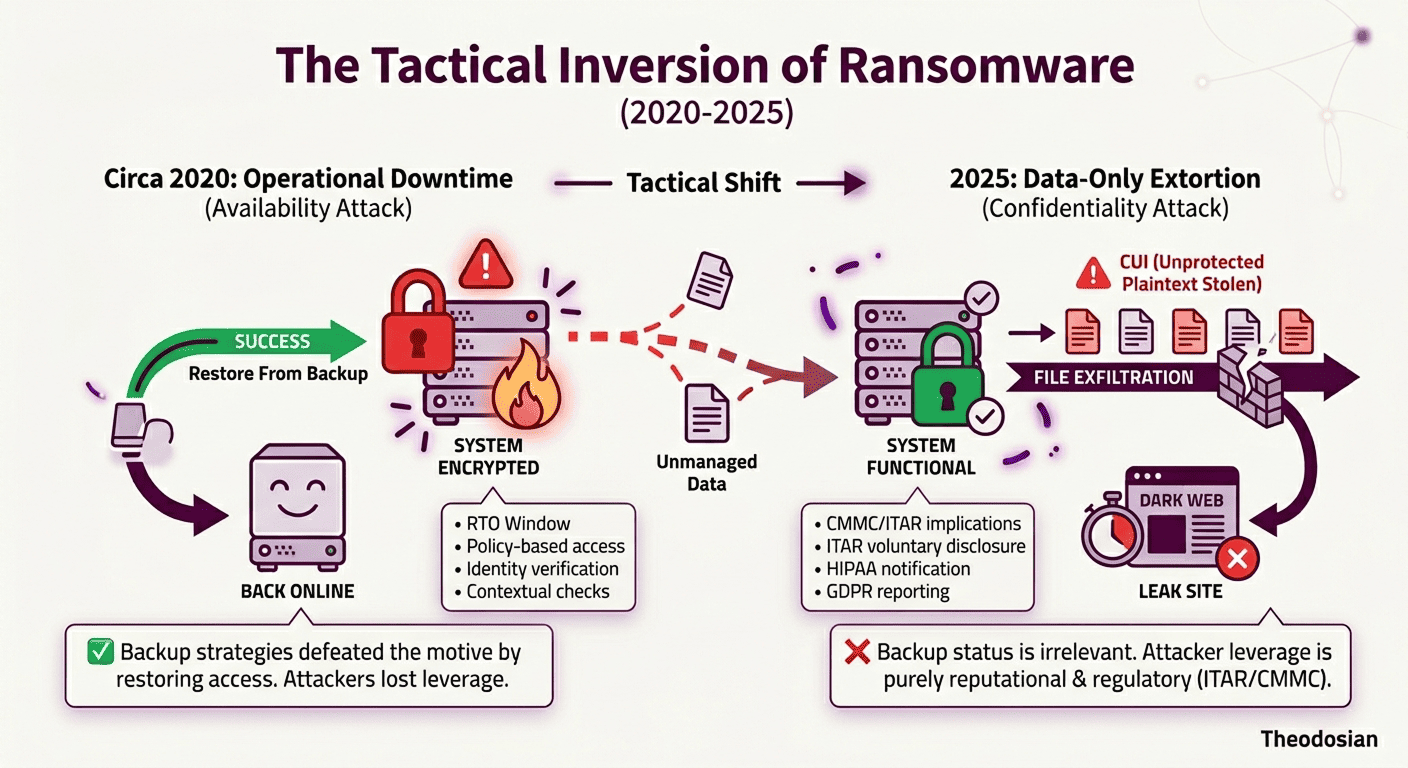
For most of ransomware's history, the leverage was operational. Encrypt the files, paralyze the business, and demand payment to restore function. Backup-centric defenses were a rational response to that model. If you could restore systems quickly from a clean copy, the attacker would lose their leverage.
The industry caught up. Organizations improved their backup posture. Immutable backups, tested recovery procedures, and air-gapped copies became standard practice in mature security programs.
Ransomware gangs noticed. Their response was to abandon the part of the attack that backups could defeat.
The exfiltration-only model removes encryption from the equation entirely. Attackers compromise the environment, move laterally, identify the most sensitive files — employee records, customer data, financial documents, technical drawings, legal correspondence — and exfiltrate them before anyone knows they're in. Then they demand payment. Not to decrypt anything. To not publish.
Sophos' State of Ransomware 2025 report found that file encryption appeared in only 50% of enterprise ransomware attacks — the lowest rate in six years, down from 70% in 2024. In manufacturing, encryption occurred in just 40% of attacks. The trend line is clear: encryption is becoming optional.
🛡️ Stolen data Is Only Leverage If It’s Readable
If an attacker exfiltrates your files tonight, can they actually use them? Ensure your data stays locked and inaccessible the moment it leaves your environment.
Why Data Recovery Fails as a Defense Against Extortion-Only Attacks
It's worth being precise about what a backup actually solves and what it doesn't.
Backups address operational continuity. If your files are encrypted, a good backup means your systems are back online within your RTO window. That's real value — it eliminates the ransom as a lever to restore operations.
Backups do nothing for data confidentiality. If your files were exfiltrated before or during an attack, a clean backup doesn't make them unexported. The copies exist on the attacker's infrastructure regardless of what you restore from. Every piece of data that left your environment is still gone; you've just also got a working copy of your systems.
The leverage in a pure exfiltration attack isn't operational downtime. It's the threat of publication. And there is no backup strategy that can un-leak data.
Consider three recent cases. PowerSchool, in December 2024, was hit with a data-only extortion attack targeting student and teacher records. Their systems remained functional throughout — there was no encryption. They paid the ransom to prevent publication despite having no operational need to do so. UnitedHealth Group paid $22 million following the Change Healthcare attack, not because they couldn't restore operations, but because 6TB of confidential patient and financial records had already been exfiltrated. Synnovis faced a $50 million demand after the Qilin group exfiltrated sensitive patient data from NHS blood testing services and published "proof packs" showing names, dates of birth, and NHS numbers.
In each case, operational recovery was either already in place or irrelevant. The payment decision was driven entirely by what had already left the environment.
CMMC, ITAR, and HIPAA: The Regulatory Fallout of Data Theft vs. Encryption
For organizations in regulated industries, the data exfiltration problem has a second dimension that makes it significantly worse.
Regulatory frameworks governing sensitive data don't distinguish between encrypted-and-recovered and exfiltrated-and-unrecovered. If the data was accessed, the notification obligation exists.
Under HIPAA, a breach of protected health information triggers a notification requirement to HHS and to affected individuals within 60 days, regardless of whether systems were restored. The determination is based on whether the data was acquired or accessed by an unauthorized person — not on whether operations recovered.
Under CMMC, a contractor that suffers a cyber incident affecting CUI is required to report to the DoD within 72 hours via the DIBNet portal. The report obligation is triggered by the incident itself, not by whether encryption occurred. A contractor with pristine backups and a four-hour recovery time still has a reporting obligation if CUI was exfiltrated.
Under ITAR, an unauthorized export of export-controlled technical data — even an inadvertent one via exfiltration — may constitute a violation that triggers voluntary disclosure obligations to the Directorate of Defense Trade Controls. The backup status of your systems is not a defense.
The operational and regulatory problems are separate. Backup addresses the first. It does not address the second.
The ROI of Data Theft
Understanding why this model has proliferated helps explain why it won't go away.
CL0P is the clearest case study. In May 2023, the group exploited a zero-day in the MOVEit Transfer platform, installing a web shell to exfiltrate data from thousands of organizations. The attack affected over 2,600 companies and 77 million individuals. CL0P made no attempt to encrypt anything. They relied entirely on the threat of data publication, and the campaign generated an estimated $75–100 million in ransom payments before it concluded.
The economics of pure exfiltration are attractive for several reasons. Encryption triggers endpoint detection tools that file exfiltration doesn't always catch. Operational outages at a target organization create noise — incident response teams, law enforcement involvement, public coverage — that exfiltration can avoid for weeks. And data auctions allow attackers to monetize the stolen material even when targets refuse to pay. REvil pioneered dark web data auctions in 2020; by 2025, multiple active groups were operating auction-based extortion models as a standard alternative to ransom negotiation.
Unit 42's Q1 2025 extortion report found that in one in five cases, data exfiltration occurred in under an hour. In one in four cases, it was complete within five hours. The mean dwell time before detection remains over 200 days. In the average environment, attackers had the data they needed before anyone knew they were in the building.
Understanding Double and Triple Extortion Strategies
Pure exfiltration is the current dominant model, but the broader trend is multi-vector extortion that compounds the pressure.
Double extortion combines data theft with encryption: two separate demands, two separate failure modes, two separate restoration paths needed. Even organizations with strong backup posture still face the publication threat.
Triple extortion adds a third pressure layer — typically DDoS attacks against the target organization's infrastructure, direct harassment of their customers or partners, or public disclosure campaigns on social media. The logic is escalation: if a target refuses payment after encryption and a leak threat, the next tool is direct damage to their customer relationships.
For defense contractors and regulated enterprises, the threat geometry is particularly difficult. A CMMC-scoped contractor facing a data exfiltration threat has to simultaneously manage the DoD 72-hour incident reporting clock, assess whether export-controlled technical data was included in the exfiltrated material, determine ITAR voluntary disclosure obligations, notify affected parties, and handle the external ransom negotiation — all while the attacker's public countdown timer is running.
None of that is solved by being able to restore from backup.
Using File-Level Protection to Devalue Stolen Data
The answer to exfiltration-based extortion is not better backup. It's making the exfiltrated data worthless.
This is the core premise of data-centric security: protection that travels with the file, not the network perimeter around it. When every file carries its own per-file FIPS 140-3 validated encryption and its own access policy, an attacker who successfully exfiltrates documents cannot access data without passing contextual checks. There is nothing to publish. The leverage is gone.
This framing is important: Theodosian doesn't prevent data from leaving your environment — no security product can guarantee that. What it does is ensure that data leaving your environment is encrypted in a way that makes it unusable without valid authorization. The extortion model depends on having something damaging to threaten publication of. Context-aware access controls remove that. Even if an attacker exfiltrates a file, access to the plaintext requires passing identity verification, device trust checks, and location-based policy conditions that the attacker cannot satisfy.
Backup addresses what happens after an incident. File-level protection addresses what the attacker gets during one.
What This Means for Your Security Stack Today
The exfiltration trend doesn't make backup less important; it makes it insufficient on its own. A mature posture addresses both operational recovery and data confidentiality. The practical question is whether your current controls do both.
A few questions worth answering:
- If an attacker exfiltrated your most sensitive files tonight, would they be encrypted at the file level, or just protected by your network perimeter?
- Can you revoke access to an exfiltrated document after the fact, or does the exfiltration end your ability to control the data?
- Do your incident response plans distinguish between the operational recovery timeline and the regulatory notification timeline? They're separate clocks.
- Have you mapped which categories of data in your environment are subject to ITAR, CMMC, or HIPAA notification obligations if exfiltrated?
The organizations that are most exposed are those whose security investments are concentrated in detection and recovery — tools that are designed to respond to an attack after files have already left. Protection at the file level changes what an attacker gets.
🛑 Make Exfiltrated Data Worthless
Don't just detect the theft, defeat the motive. If an attacker can't pass the contextual handshake, they can't see the data. It’s that simple.
FAQs: Data Exfiltration & Ransomware
What is exfiltration-only ransomware?
Exfiltration-only ransomware (also called data extortion or pure exfiltration attacks) is an attack model where attackers steal sensitive files from an organization and demand payment to suppress their publication, without encrypting any systems. There is no operational downtime, no encrypted files to decrypt. The leverage is entirely reputational and regulatory: pay, or we publish your data.
Why can't backups stop exfiltration ransomware?
Backups restore systems and files to a clean state — it addresses operational continuity after an encryption-based attack. It cannot undo data exfiltration. If files were copied to an attacker's infrastructure before you restored from backup, those copies still exist. Backup eliminates the operational leverage in an encryption attack; it does not affect the publication-threat leverage in an exfiltration attack.
What is double extortion ransomware?
Double extortion combines data theft with system encryption. Attackers exfiltrate sensitive files first, then encrypt the victim's systems. The ransom demand covers both: decrypt the systems AND don't publish the data. Victims face two separate failure modes. Even organizations that restore from backup are still exposed to the publication threat. Double extortion has been the dominant ransomware model since approximately 2019.
What compliance obligations are triggered by ransomware data exfiltration?
This depends on the type of data involved. For HIPAA-covered organizations, a breach of protected health information (PHI) triggers notification obligations to HHS and affected individuals within 60 days of discovery, regardless of whether systems were restored. For DoD contractors, a cyber incident affecting CUI requires a 72-hour report to the DoD via DIBNet. For organizations handling ITAR-controlled technical data, unauthorized access may trigger a voluntary disclosure obligation to the DDTC. Backup recovery does not satisfy these obligations — the triggering event is the unauthorized access, not the system state.
How does per-file encryption help against data exfiltration attacks?
Per-file encryption shifts the security from the perimeter to the document itself. Each file is protected by its own unique cryptographic key and a real-time, context-aware access policy.
If an attacker exfiltrates a protected file, they don't just "get ciphertext"—they get a file that refuses to open. Because the attacker cannot satisfy the contextual checks (such as verified identity, approved device posture, and geographic location), the Theodosian platform denies the access request in milliseconds.
The extortion model relies on having readable data to threaten publication. When a file refuses to decrypt, it has zero publication value. While no control can 100% guarantee that a file won't be moved, Theodosian ensures that even if it's moved, it remains inaccessible and unusable.
