The FTC Safeguards Rule requires financial institutions to protect customer information. Most compliance programs interpret that as: secure your systems, encrypt your databases, implement MFA, and conduct annual risk assessments.
That's necessary. It's not sufficient.
The Safeguards Rule doesn't limit your obligation to data inside your systems. It extends to NPI you've shared — with your accountant, your attorney, your mortgage servicer, your cloud vendor, your credit reporting integration. The moment NPI leaves your environment, your compliance obligation follows it.
Most financial institutions don't have controls on data after it's been shared. They have contracts, which aren't the same thing.
What the Safeguards Rule Requires
The FTC's updated Safeguards Rule under 16 CFR Part 314 (final amendments effective 2024) contains specific technical requirements that go beyond the "maintain a security program" framing most compliance teams focus on.
On encryption (§ 314.4(d)): Financial institutions must encrypt customer information in transit over external networks and at rest. The regulation specifies "current cryptographic standards" with "appropriate safeguards for cryptographic key material." This isn't encryption-at-rest on your core banking platform. It applies to every file containing NPI that travels anywhere.
On access controls (§ 314.4(e)): Technical and physical controls must authenticate and permit access only to authorized users, with access limited to what each user needs to perform their duties. The requirement is explicit about limiting access, not just restricting it to your organization.
On service providers (§ 314.4(f)): This is the provision most compliance programs underweight. The rule requires financial institutions to:
- Take reasonable steps to select service providers capable of maintaining appropriate safeguards
- Ensure, through contracts, that service providers implement and maintain safeguards appropriate to the nature of the information
- Periodically assess service providers based on the risk they present
The critical legal reality embedded in § 314.4(f): the obligation stays with the financial institution. The service provider doesn't absorb your compliance responsibility. You remain liable for NPI after it moves.
Is Your Compliance Program Stopping at Your Firewall?
The FTC now audits Risk Management, not just policies. If you can’t enforce encryption and access logs after a file leaves your server, you aren’t managing the risk; you’re only documenting it.
Where NPI Actually Goes
A typical community bank, credit union, or mortgage lender shares customer NPI across a wider network of third parties than most compliance programs acknowledge. The common categories:
Professional service providers: Accountants, external auditors, and tax advisors receive detailed customer financial records as part of their work. Law firms handling collections, litigation support, or loan closings receive NPI routinely. None of these environments are part of the financial institution's security perimeter, and most aren't subject to independent GLBA audits.
Operational vendors: Mortgage processors, ACH payment vendors, title companies, and loan origination software providers handle NPI to execute core transactions. Each integration point is a file transfer, and each file transfer is a potential exposure.
Credit infrastructure: Credit bureau pulls, FICO score requests, and credit monitoring services involve sending customer identifiers and financial data to third parties whose security controls you cannot directly audit.
IT and cloud vendors: Managed service providers, cloud storage platforms, and IT support vendors often have access to systems containing NPI, not always with the encryption and access controls the Safeguards Rule requires them to maintain.
Now ask a harder question: for each of those relationships, what happens to the NPI file after it's shared?
In most cases, the answer is: it gets filed, backed up, archived, and retained in systems the originating financial institution has no visibility into and no ability to control.
The File Boundary Problem
The Safeguards Rule encryption requirement applies to NPI in transit and at rest. For files transmitted between your institution and a service provider, "in transit" encryption (TLS 1.2+) is standard. "At rest" encryption at the service provider's end is required by contract, but almost never verified in practice.
After the file arrives at the service provider, there's a further layer the rule implicates but that contracts rarely address: what happens when the file is forwarded internally, downloaded to an employee's device, stored in a backup, or retained after the engagement ends?
Consider a mortgage transaction. Customer financial records — tax returns, pay stubs, bank statements, SSNs — flow to the lender, the mortgage processor, the title company, the underwriter, and potentially to the secondary market purchaser. Each party files these records, and each backup system retains them. Each employee who worked on the deal has versions on their workstations.
The originating institution signed contracts with each of those parties. It has no visibility into what any of them did with the files after the transaction closed. The NPI is still subject to the Safeguards Rule. The institution still bears responsibility.
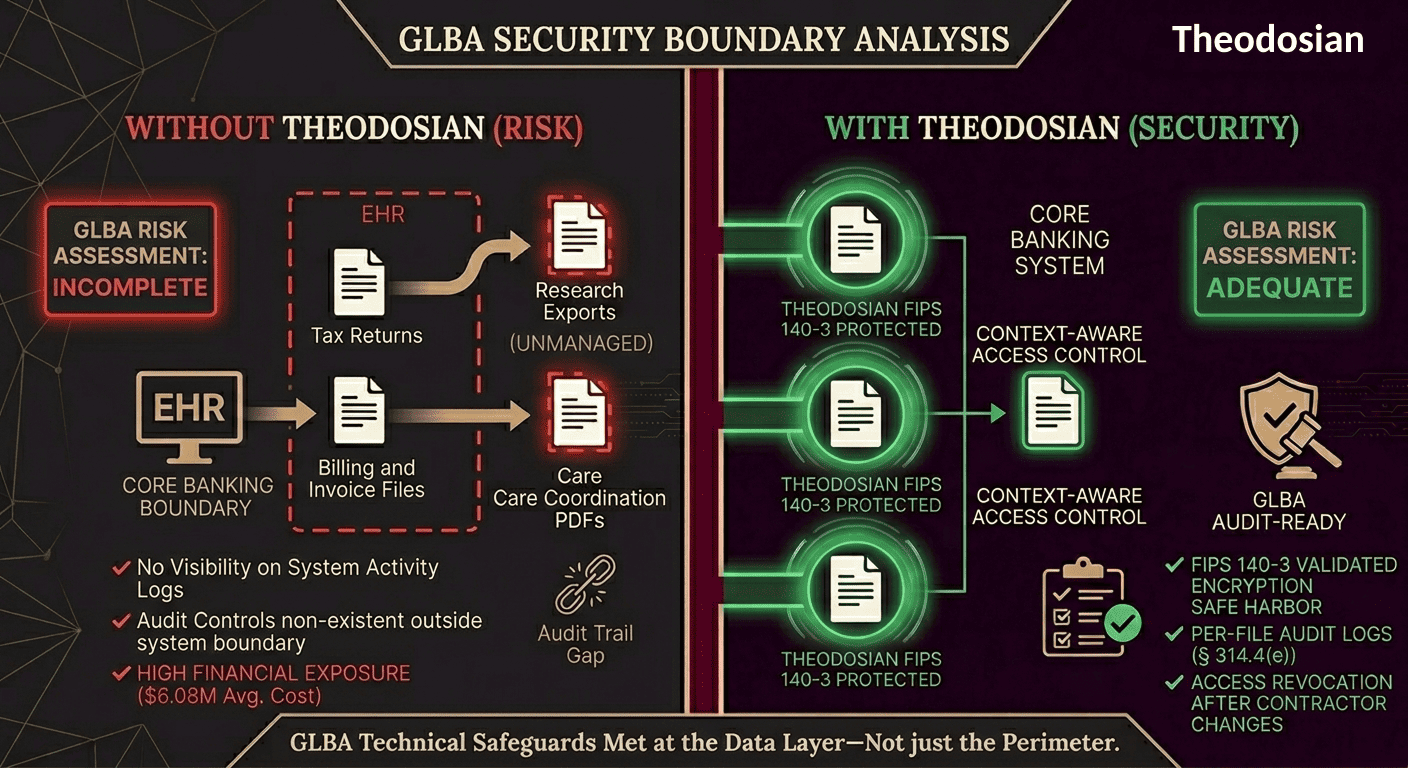
This is the gap that generates enforcement action, not because the institution failed to encrypt its own database, but because it had no mechanism to govern NPI after it left.
The Cost of Getting This Wrong
The FTC has civil penalty authority of up to $53,088 per violation per day for Safeguards Rule violations. For ongoing violations — where NPI has been improperly handled across multiple customer files over an extended period — the penalties compound.
The Blackbaud case illustrates the scale. The company's security failures led to a breach affecting 1.5 billion records across 13,000+ customers, including healthcare organizations and financial institutions. The combined penalties across FTC settlements, SEC enforcement, and state attorneys general exceeding $59 million. The FTC's settlement specifically required implementation of file-level controls, including formal encryption protocols and access control documentation — the exact gap the original failure exposed.
For financial institutions, the breach cost baseline is significant, independent of regulatory fines. The average cost of a financial services data breach was $6.08 million in 2024 (IBM Cost of a Data Breach). For a regional bank, credit union, or mortgage lender operating on tighter margins than a national institution, that figure is existential.
Community banks and credit unions already spend 3–4 times more per dollar of assets on compliance than large institutions. A Safeguards Rule violation that generates regulatory action doesn't just cost money; it consumes the operational capacity of an organization that likely doesn't have a dedicated incident response team.
Why This Is Harder for Regional and Community Financial Institutions
Large national banks have regulatory affairs teams, in-house counsel experienced in GLBA, and leverage in vendor negotiations to demand specific security contractual terms. A $200M community bank with a 3-person compliance team doesn't.
The specific challenges:
Contract leverage: Most core banking vendors, credit bureaus, and payment processors aren't negotiating their standard agreements on a per-customer basis. The security provisions they offer may not satisfy the Safeguards Rule's "appropriate safeguards" standard, but smaller institutions often don't have the leverage to require changes.
Vendor assessment capacity: The rule requires periodic assessment of service providers based on risk. For a community bank managing 40–60 vendor relationships, conducting meaningful security assessments of each is a resource commitment most compliance teams can't sustain.
Post-share visibility: Once NPI has been shared with a vendor, a law firm, or a mortgage processor, smaller institutions typically have no technical mechanism for monitoring what happens to those files. The contract says the vendor will protect the data. Whether they do is unverifiable.
Breach notification timing: The Safeguards Rule now requires notification to the FTC within 30 days of discovering a breach affecting 500 or more customers. For an institution without a dedicated security team or incident response playbook, 30 days is a very compressed timeline.
How File-Level Controls Change This
The practical gap in most financial institution compliance programs isn't the policy; it's the enforcement mechanism. Contracts require service providers to implement safeguards. They don't enforce safeguards on the files themselves.
Per-file FIPS 140-3 validated encryption closes this at the data layer. FIPS 140-3 is the cryptographic module validation standard — the specific definition of "current cryptographic standards" that the Safeguards Rule references in § 314.4(d). Every NPI file shared with an external party carries its own cryptographic key and access policy. That policy travels with the file regardless of where it goes — whether it's retained in a vendor's archive, forwarded internally, or backed up on a system the originating institution has never audited.
The specific compliance benefits:
Satisfies § 314.4(d) encryption requirements at the file level using FIPS 140-3 validated encryption — not just in transit and at-rest on your own systems, but for the file wherever it exists.
Access can be revoked after sharing. If a service provider relationship ends, or if a breach is suspected at a vendor, access to all NPI files shared with that vendor can be revoked immediately — the files become inaccessible without active reconfiguration of the access policy. This is the kind of control that satisfies the "reasonable steps" standard in § 314.4(f).
Per-file audit logs provide evidence of access activity on NPI files regardless of what system they're stored in. For FTC examination purposes, this is the documentation trail that demonstrates the safeguards are operational, not just documented.
The breach notification exposure changes. If a vendor is compromised and files are exfiltrated, encrypted NPI files are ciphertext to the attacker. The Safeguards Rule's breach notification obligation applies to "customer information in a covered system." Properly encrypted files that are exfiltrated and remain inaccessible to the attacker substantially reduce the scope of reportable breach.
This approach supports compliance with the FTC Safeguards Rule's data security requirements — specifically the encryption, access control, and service provider oversight provisions — at the layer where most violations actually occur.
The GLBA Safeguards Rule Compliance Checklist
The questions below map to the specific provisions of 16 CFR Part 314 most frequently associated with FTC enforcement action. Use them to identify where your institution's NPI protection ends after data is shared.
- Does your information security program explicitly address NPI that has been shared with service providers — or does it focus primarily on data inside your own systems?
- Do your service provider contracts include specific language requiring encryption of NPI at rest and in transit, aligned with "current cryptographic standards"?
- Do you conduct periodic assessments of service providers' actual security posture — not just collect attestations?
- When a service provider relationship ends, is there a verified process for ensuring NPI files are deleted or returned, and can you confirm deletion occurred?
- Are files containing NPI encrypted at the file level when transmitted to service providers — not just encrypted in transit?
- Do you have access logs covering NPI files shared externally, or only logs covering your own systems?
- If a service provider suffered a breach today, could you identify every NPI file they held from your institution and revoke access to those files?
- Does your breach notification protocol address the 30-day FTC reporting timeline for incidents affecting 500+ customers, including incidents originating at third parties?
If the answers to the last four questions are "no" or "not currently," those represent the specific gaps the Safeguards Rule targets in § 314.4(d), (e), and (f) — and the gaps most likely to generate FTC enforcement attention.
Make Data Exposure a Non-Event
When NPI is encrypted at the file level, a vendor breach or a lost laptop doesn't have to be a reportable event. It stays a contained security incident, not a liability costing millions. Secure the data, not just the perimeter.
FAQs: GLBA Safeguards Rule and File Security
Who does the GLBA Safeguards Rule apply to?
The FTC Safeguards Rule under 16 CFR Part 314 applies to "financial institutions" as defined under GLBA — a category that includes not just banks and credit unions, but mortgage lenders and brokers, auto dealers offering financing, tax preparers, financial advisors, debt collectors, and any business "significantly engaged" in providing financial products or services. If your business collects, maintains, or processes customer financial information, the Safeguards Rule likely applies.
Does the Safeguards Rule require encryption?
Yes. Under 16 CFR § 314.4(d), financial institutions must encrypt customer information in transit over external networks and at rest, using "current cryptographic standards" with appropriate key management safeguards. This applies to NPI wherever it exists, not only within your own systems. Files shared with service providers remain subject to this requirement.
What does the Safeguards Rule require for service provider relationships?
Under 16 CFR § 314.4(f), financial institutions must: take reasonable steps to select service providers capable of maintaining appropriate safeguards; ensure through contracts that service providers implement and maintain those safeguards; and periodically assess service providers based on the risk they present. Critically, the financial institution retains liability — entering into a contract with a service provider does not transfer your compliance obligation.
How does the 30-day breach notification requirement work?
The 2024 amendment to the Safeguards Rule requires financial institutions to notify the FTC within 30 days of discovering a security breach affecting customer information of 500 or more customers. This applies to breaches at the financial institution itself and at service providers holding the institution's customer data. Third-party service providers are contractually required to notify the financial institution "as soon as possible" after discovering a breach — but a 30-day clock starts from your discovery, regardless of when the vendor notifies you.
What makes the Safeguards Rule particularly challenging for community banks and credit unions?
Smaller institutions typically manage 40–60 or more vendor relationships with limited compliance staff, have less leverage in vendor contract negotiations to demand specific security provisions, and spend proportionally more on compliance — 3–4x more per dollar of assets than large national banks. The Safeguards Rule's ongoing monitoring requirements for service providers are operationally demanding for organizations without dedicated security teams, and the 30-day breach notification timeline is a compressed window for institutions without incident response infrastructure.
