Here is the examination question FFIEC examiners have been asking financial institutions since 2024: "Walk me through how customer data is protected when it's shared with an external service provider." The institution answers: "We encrypt at rest and in transit." The examiner follows up: "What happens to the file after it's delivered to the service provider's system?" The room goes quiet.
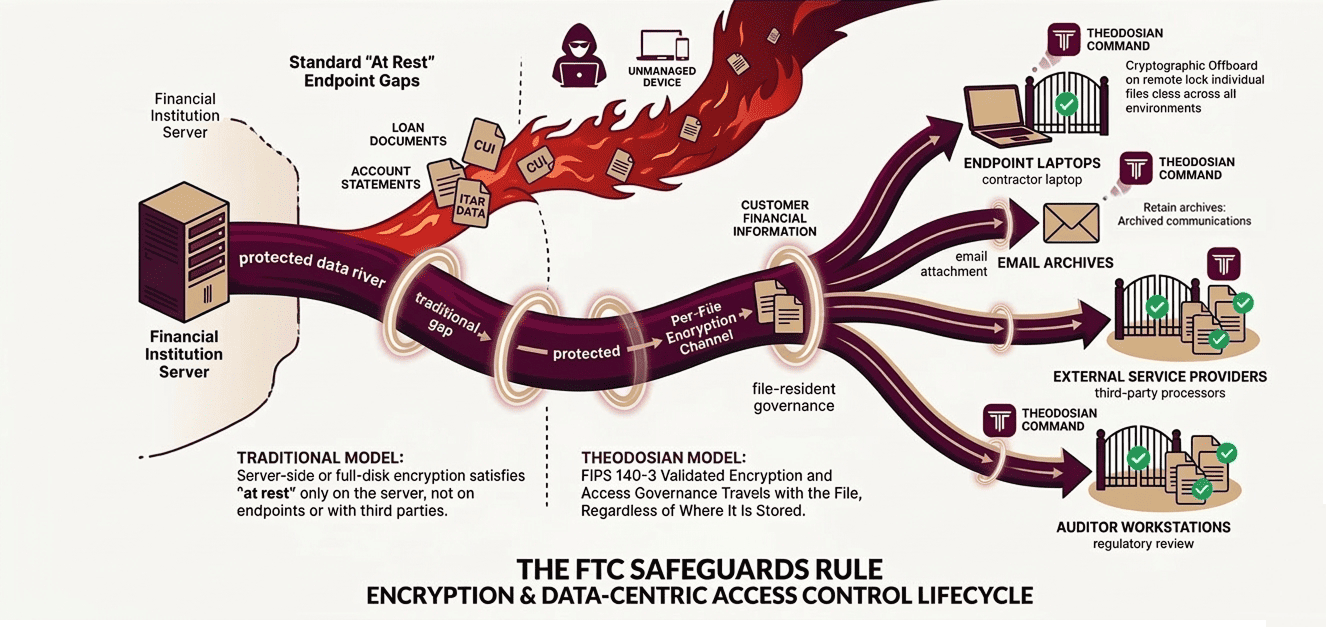
That silence is where most FTC Safeguards Rule compliance gaps actually live. The Safeguards Rule (16 CFR Part 314) requires financial institutions to protect customer financial information from unauthorized access, and "at rest" under the rule means any state in which data is stored. That includes files on employee endpoints. Files in email archives, files on service provider systems, and files on external auditor workstations. Server-side encryption satisfies "at rest" on the server. It says nothing about where the file is when it's not on the server.
The FTC has made this interpretation explicit. The penalty for non-compliance is $53,088 per violation per day. Combined FTC enforcement actions in 2024–2025 exceeded $100 million. FFIEC examiners now cite "inadequate protection of unstructured data at-rest" as a standard finding pattern. The compliance gap is not a theoretical risk; it is the dominant examination finding in the current enforcement cycle.
🛡️ Is Your "At Rest" Encryption Leaving You Exposed?
If customer data exists on an employee's laptop or in a service provider’s inbox without your control, you aren't compliant. In 14 days, we can show you how to extend your encryption boundary to every file, on every device.
Who the FTC Safeguards Rule Actually Covers
The Safeguards Rule covers "financial institutions" under GLBA. The definition is broader than most compliance teams initially recognize.
| Organization Type | In-Scope? |
|---|---|
| Banks and credit unions regulated by federal banking regulators | Covered under parallel banking regulations (OCC, FDIC, NCUA)—Safeguards principles apply |
| Mortgage brokers, lenders, and servicers | Yes—collects and processes customer financial information |
| Investment advisers (non-SEC-registered) and tax preparers | Yes—directly covered under FTC jurisdiction |
| Accounting firms handling client financial data | Yes—"receives" customer financial information from financial institutions |
| Auto dealers providing financing | Yes—specifically included in the FTC Safeguards Rule scope |
| HR and payroll platforms handling employee financial data | Potentially—depends on data collected and processing role |
The "receives" element catches organizations that don't consider themselves financial institutions. An accounting firm that receives client tax returns, financial statements, and investment records from a financial institution is handling "customer financial information" under the rule, even though it is providing professional services, not financial products.
The Three Most Common Safeguards Rule Implementation Failures
Failure 1: Server-side encryption misread as "at rest" compliance
The Safeguards Rule requires encryption of customer financial information "at rest." Most financial institutions and their compliance teams interpret this as server-side database encryption or full-disk encryption on servers. This interpretation satisfies "at rest" for data that stays on the server. When a file is downloaded to an employee's laptop, emailed to an auditor, or transferred to a service provider, it leaves the server-side encryption environment. The file is now "at rest" on an endpoint, in an email archive, or on a third-party system, and the server-side encryption provides no protection there.
Failure 2: Service provider contracts that don't address file-level protection
The Safeguards Rule requires financial institutions to oversee their service providers' security and contractually require them to implement appropriate safeguards (16 CFR § 314.4(f)). In practice, most service provider agreements address data breach notification and general security standards, but do not specify how the service provider must protect files received from the institution. The institution delivers encrypted files in transit. The service provider decrypts them on receipt and stores them in their own environment, which may not have equivalent encryption standards. The institution's compliance obligation does not end at delivery.
Failure 3: The qualified individual accountability vacuum
The Safeguards Rule requires financial institutions to designate a qualified individual (QI) responsible for the information security program (16 CFR § 314.4(a)). The QI is responsible for reporting to the board annually. In examinations, regulators find that the QI role exists on paper but lacks the actual visibility needed to fulfill it: no centralized view of where customer data resides, no audit trail of file access beyond the primary system, no mechanism to verify that service provider handling meets the contractual standard.
What the FFIEC Examination Pattern Tells You About Enforcement Direction
FFIEC examiners have established a consistent examination pattern for Safeguards Rule and GLBA compliance in 2024–2025 cycles. The pattern reveals where enforcement focus is heading:
Examiners are asking specifically about unstructured data—files, documents, spreadsheets—as distinct from database records. The question "how do you encrypt customer data at rest in your core banking system?" has been supplemented by "how do you protect customer files that are downloaded, emailed, or shared with service providers?"
Examination findings increasingly cite: file-sharing practices with law firms and accounting firms, employee remote access (files on personal or unmanaged devices), and vendor file handling (files delivered to service providers and auditors). These are the shadow data vectors—authorized file transfers with no post-transfer governance—that standard database encryption doesn't address.
The FTC's June 2025 enforcement guidance reiterated that the encryption requirement applies to all forms of data storage, explicitly including endpoint devices and third-party environments where customer data is transmitted. Institutions that interpreted "at rest" narrowly as server-side encryption are being asked to demonstrate coverage for the full data lifecycle.
Building Safeguards Rule Compliance Without Rebuilding Your Stack
Closing the Safeguards Rule encryption gap does not require replacing existing infrastructure. It requires adding a layer that server-side encryption was never designed to provide: encryption and access governance that travels with the file after it leaves the server.
These are five implementation areas that close the FFIEC examination gap:
1. Per-file encryption for customer data files
Files containing customer financial information, loan documents, account statements, tax records, and audit packages should be encrypted at the file level, not just at the server level. Per-file encryption using FIPS 140-3 validated modules means the file is encrypted wherever it resides: on an employee endpoint, in an email archive, on an auditor's system, or in a service provider's storage environment.
2. Access policy that survives transfer
The access policy governing a customer file should travel with the file. When the file is shared with an external auditor, the policy should define who at the auditing firm can access it, from which devices, and until what date. When the audit closes, access should be revocable, regardless of where the file resides.
3. Service provider file governance in contracts and in practice
The service provider oversight requirement (§ 314.4(f)) needs to be satisfied in practice, not just in contract language. This means verifiable evidence that files delivered to service providers remain protected, not a representation from the service provider that they have encryption standards.
4. Endpoint coverage for remote and hybrid environments
Files downloaded to employee endpoints during remote work are "at rest" on those endpoints under the Safeguards Rule. Endpoint encryption coverage must extend to files actively in use, not just files on managed devices connected to the corporate network.
5. Audit log for the qualified individual's annual board report
The QI annual report to the board (§ 314.4(a)) requires substantive information about the security program's effectiveness. A per-file access audit log that shows who accessed what, when, from where, and under what policy conditions gives the QI actual visibility, not just a representation that policies exist.
Close the Gap Before the Next Examination Cycle
The FTC Safeguards Rule's encryption requirements cover every location where customer financial information is stored, including locations that server-side encryption was never designed to govern. FFIEC examiners are now asking exactly this question. The examination finding "inadequate protection of unstructured data at-rest" has become a standard citation, not an edge case.
Theodosian secures the data layer the Safeguards Rule requires: per-file FIPS 140-3 validated encryption that travels with the file, access governance that survives transfer to service providers and auditors, and a per-file audit log that gives your qualified individual the visibility needed for the board's annual report.
🤖 Give Your Board a Report with Teeth
Partner with Theodosian to implement FIPS 140-3 validated, file-resident governance. In just 14 days, you'll have the visibility and revocation power the Safeguards Rule demands.
FAQs: FTC Safeguards Rule and Encryption at Rest
Does the FTC Safeguards Rule require file-level encryption, or is server-side encryption sufficient?
The Safeguards Rule requires encryption of customer financial information "in transit and at rest" (16 CFR § 314.4(e)(3)). The FTC's interpretation, reinforced by June 2025 enforcement guidance, extends "at rest" to all locations where customer data is stored—including employee endpoints, service provider systems, email archives, and external audit environments. Server-side encryption satisfies "at rest" only for data that remains on the server. Files that have been downloaded, emailed, or transferred to third parties are "at rest" in their new location—and server-side encryption provides no protection there. FIPS 140-3 validated per-file encryption satisfies the requirement across all storage environments.
Which organizations are covered by the FTC Safeguards Rule?
The Safeguards Rule covers financial institutions subject to FTC jurisdiction under GLBA, a category that is broader than bank-regulated entities. It includes mortgage brokers and lenders, investment advisers not regulated by the SEC, tax preparers, auto dealers that provide or broker financing, and other non-bank financial institutions that collect customer financial information. Critically, organizations that "receive" customer financial information from financial institutions, including accounting firms, law firms handling financial matters, and HR platforms, may also fall within scope depending on their data handling practices. Federal banking agencies (OCC, FDIC, NCUA, Federal Reserve) enforce parallel requirements under the Interagency Guidelines for banks and credit unions.
What does the FTC's service provider oversight requirement mean in practice?
The Safeguards Rule (§ 314.4(f)) requires financial institutions to select and retain service providers that maintain appropriate safeguards, and to contractually require those safeguards. In practice, this means:
1. Contracts must specifically address how service providers protect customer files they receive, not just general data breach standards.
2. The institution must have a mechanism to verify compliance, not just a contractual representation
3. When a service relationship ends, files delivered to the service provider must be retrievable or rendered inaccessible. Per-file encryption with access revocation provides a verifiable mechanism: the institution can demonstrate, via audit log, what files were accessed by the service provider, and can revoke access when the relationship ends.
What is the penalty for FTC Safeguards Rule non-compliance?
Civil penalties under the FTC Act are $53,088 per violation per day (adjusted annually for inflation). The penalty is per violation; multiple instances of inadequately protected customer files can be counted as multiple violations. Combined FTC enforcement actions in 2024–2025 exceeded $100 million. The FTC Act also permits injunctive relief, requiring organizations to implement specific remediation steps under regulatory oversight. Separately, state attorneys general have authority to enforce GLBA Safeguards Rule violations affecting state residents, creating a parallel enforcement channel. The most significant risk, however, is often reputational: the FTC publishes enforcement actions.
How does the FTC Safeguards Rule relate to banking regulator examination requirements?
Banks and credit unions are regulated by the OCC, FDIC, Federal Reserve, and NCUA under parallel Safeguards requirements derived from the same GLBA authority. FFIEC examination guidance, which coordinates examination standards across these regulators, has established consistent examination patterns for Safeguards compliance since the amended rule became effective in April 2024. FFIEC examiners are currently focusing on unstructured data governance: specifically, how institutions protect files shared with service providers, accessed by remote employees, and transmitted to external parties. The examination question "how do you protect customer data on employee endpoints and with service providers?" is now a standard part of information security examination, not an advanced or specialized inquiry.
