If you’re responsible for compliance or security, few questions create more confusion than: “Are we governed by ITAR or EAR?”
The wrong answer can mean over-restricting your business, or worse, unknowingly committing a federal violation.
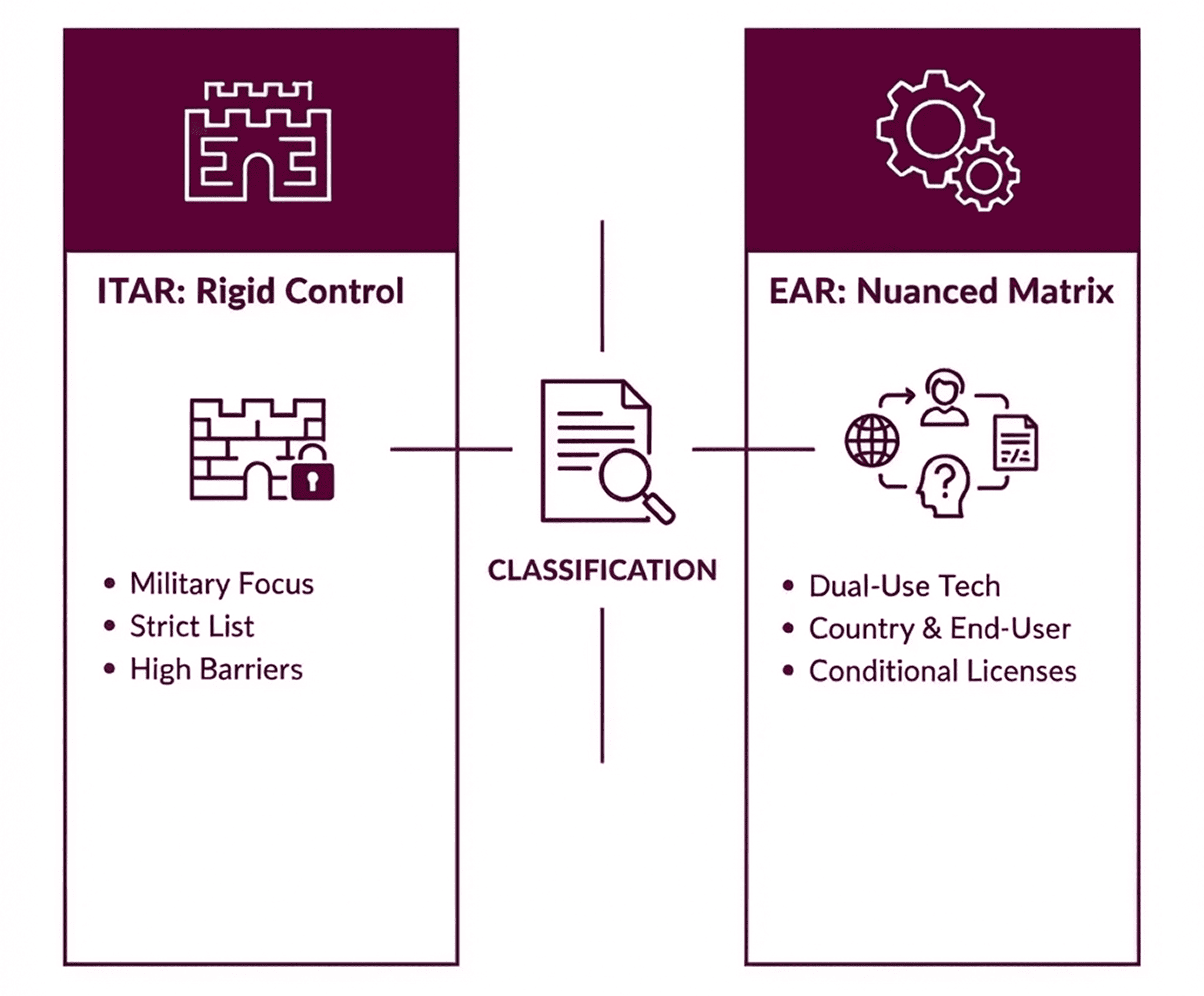
ITAR vs EAR at a High Level
Both ITAR and EAR exist to prevent sensitive U.S. technology from reaching hostile actors. But they differ in scope, strictness, and enforcement philosophy.
ITAR (International Traffic in Arms Regulations):
- Regulated by the Department of State
- Covers military and defense-specific items
- “No” by default - access is tightly restricted
- Applies to weapons systems, military components, and space technologies
EAR (Export Administration Regulations):
- Regulated by the Department of Commerce
- Covers commercial and dual-use technology
- “Maybe” by default - rules vary by country and end use
- Applies to a far broader range of businesses
📈 Build a Growth-Ready Compliance Program
Learn how to move away from manual "log chasing" and toward an automated, data-centric model that satisfies both State and Commerce Department auditors.
The Biggest Practical Difference: Who Can Access the Data
For ITAR, access is limited to U.S. Persons only (citizens and permanent residents).
For EAR, access rules depend on:
- Data classification
- The user’s nationality
- The destination country
- Intended use
This means EAR violations often occur internally, not externally.
The Overlap CISOs Miss: Deemed Exports
Both regulations share one of the most misunderstood rules in export control: the Deemed Export Rule.
If a foreign national accesses controlled technical data, even inside your office or cloud environment, the U.S. government considers that an export to that person’s home country.
No shipment required.
No malicious intent required.
A server log showing access is enough.
This is why traditional perimeter security fails to address export compliance risk.
Why Misclassifying EAR Is So Dangerous
Misclassifying ITAR data as EAR can lead to catastrophic exposure. Misclassifying EAR data as uncontrolled leads to silent violations.
And classification mistakes often compound over time as:
- Files are copied
- Projects evolve
- Teams expand globally
If you’re still unclear on where EAR ends and ITAR begins, start with our foundational guide on what EAR compliance is and who it applies to.
What This Means for Security Architecture
Export compliance isn’t just a legal concern; it’s an engineering challenge. To satisfy both EAR and ITAR, your security stack must transition from defending the "pipe" to defending the "payload."
Modern controls must:
- Bind identity to the file: Automatically enforce citizenship requirements at the point of access.
- Enable persistent oversight: Ensure protection and logging persist even after data leaves your internal environment.
- Automate the audit trail: Generate real-time evidence of compliant access for regulatory review.
This architectural shift ensures that controlled data remains secure and auditable, regardless of where it is stored or who is attempting to access it.
🔒 Control Your Export Data in Real-Time!
See how Theodosian turns these complex rules into automated, identity-aware access controls that follow your data everywhere.
FAQ: EAR vs ITAR Compliance
What is the primary difference between ITAR and EAR?
Does file encryption satisfy EAR vs ITAR requirements?
While encryption is a core requirement, it must be part of a broader "data-centric" program. Under both EAR and ITAR frameworks, you must ensure that only authorized U.S. persons or licensed foreign nationals can access the keys or the unencrypted data.
How do I know if my data is ITAR or EAR?
You must check the U.S. Munitions List (ITAR) first. If your item is not there, check the Commerce Control List (EAR) for a specific ECCN. If you are still unsure, you can file a Commodity Jurisdiction (CJ) request with the State Department to settle the ITAR vs EAR compliance question definitively.
