The C3PAO doesn't care how long you've been working on it. They care what the evidence shows on assessment day.
The prevailing reality of CMMC Level 2 is that many assessment failures aren't just about missing paperwork; they are implementation failures of the tools themselves. While most contractors have basic security, they lack the granular access controls and persistent encryption required to protect CUI once it leaves a server. If you can’t enforce (and prove) access control at the file level, you aren't just failing a policy; you are failing the core NIST SP 800-171 requirements that CMMC is built upon.
With ~80,000 companies needing CMMC Level 2 certification, the stakes are existential. Industry analysts project that 33,000–44,000 companies will exit the defense market by 2027 rather than achieve certification. For many, achieving certification is viewed as prohibitively difficult, primarily from a cost perspective. Between expensive infrastructure upgrades and the high price of "gap-filling" consultants, many subcontractors feel priced out of the market.
This financial burden is usually the result of trying to 'force' legacy architecture to meet modern federal standards. This 'force-fitting' creates a critical gap: aging tools simply cannot produce the FIPS 140-3 validated evidence or real-time revocation that a C3PAO demands. To bridge this gap with legacy tech, subcontractors often face a total network redesign—unless they find a way to secure the data itself.
🛡️ From "Prohibitively Difficult" to Audit-Ready
Discover how a data-centric approach simplifies NIST SP 800-171 enforcement and slashes the cost of CMMC Level 2 compliance.
Deploy in weeks, achieve C3PAO readiness in 1-3 months.
The Three Forms of CMMC Assessment Failure
Assessment failures cluster into three categories. Understanding which type applies to your organization determines how you close the gap.
- Documentation Without Evidence: The policy exists, the SSP says the control is implemented. But the C3PAO asks for evidence — logs, screenshots, configuration exports — and the team goes silent or produces documents that don't match what's running in production. The SSP says MFA is enforced on all systems. The assessor checks and finds three legacy servers excluded from the MFA policy. That's a finding.
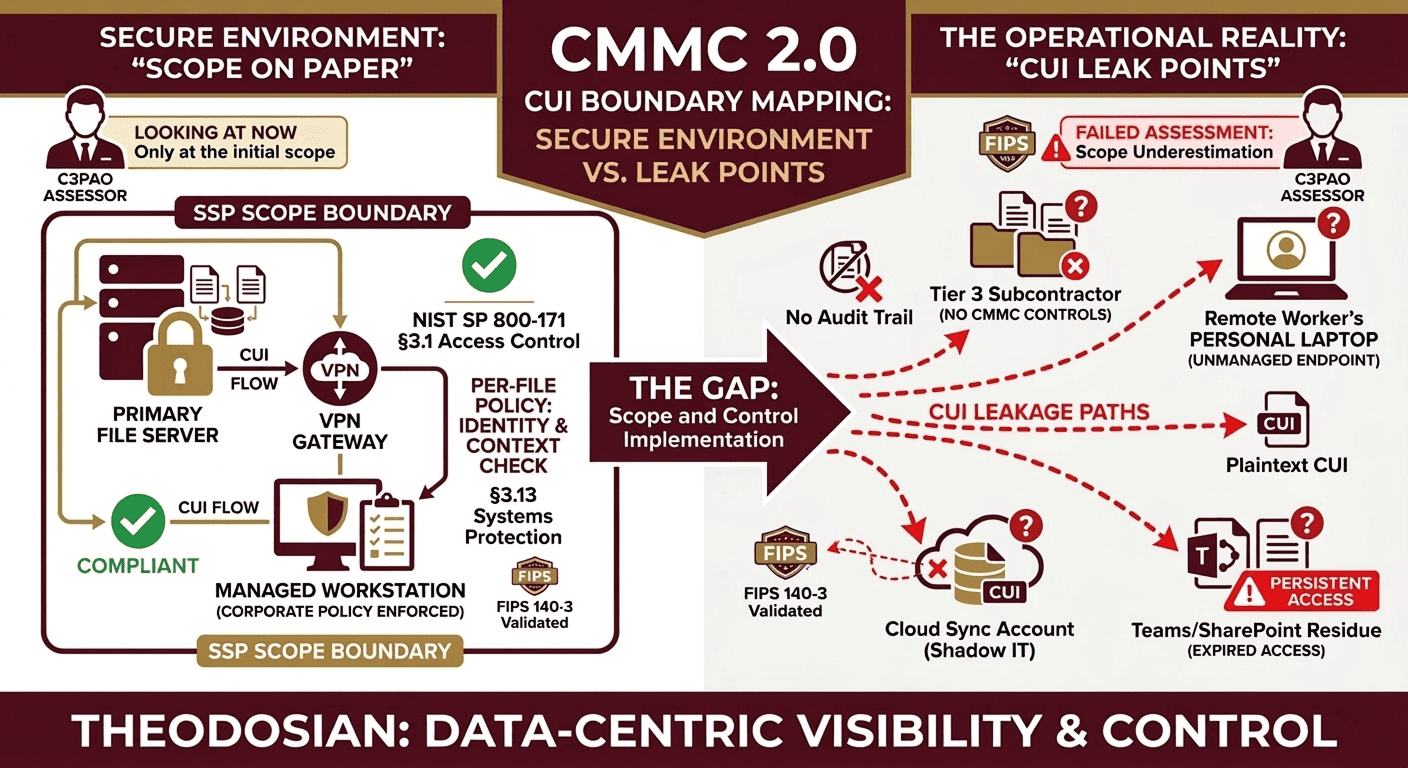
- Scope Underestimation: The CUI boundary is smaller on paper than in practice. A subcontractor's SSP covers the primary file server and the VPN. It doesn't cover the engineer's personal laptop that has design documents on it, or the cloud storage account the PM uses to share files with the customer. Every system, device, or service that touches CUI falls within the CMMC scope. If it's not in the SSP, it's a gap.
- Control Implementation That Doesn't Map to Practices: CMMC Level 2 has 110 practices across 14 domains. The most common gap is controls that partially satisfy a practice, not zero implementation, but implementation that doesn't meet the specific language of NIST SP 800-171. Control 3.13.10 (FIPS-validated encryption) is among the most cited deficiencies: organizations use encryption, but not FIPS 140-3 validated modules, which is the specific requirement.
Control Family 3.13: The Encryption Requirement That Trips Most Contractors
NIST SP 800-171 Control 3.13.10 requires FIPS-validated cryptography when protecting CUI. This is not "encryption" generically; it requires NIST CMVP-validated encryption modules. BitLocker in certain configurations qualifies. Many popular file sync and collaboration tools do not. Most encrypted email products do not enforce FIPS 140-3 validated modules.
The practical implication: if CUI is shared via an email attachment with a subcontractor, and that email tool is not FIPS 140-3 validated, that's a gap under 3.13.10. If design files are stored in a cloud sync folder not covered by a FIPS-validated encryption module, that's a gap. The control is specific, and assessors test it with specificity.
Per-file encryption using FIPS 140-3 validated modules closes 3.13.10, but only if the SSP documents the specific module, version, and deployment scope. The evidence package for 3.13.10 should include the CMVP certificate number, deployment configuration, and system coverage.
The CUI Boundary Problem: What's In Scope and What Gets Missed
The CMMC assessment scope is defined by where CUI lives, travels, and is processed. Most contractors underestimate this boundary in three ways:
First, subcontractor data flow. When CUI is shared downstream to Tier 3 suppliers, those file transfers fall within your CUI handling obligations. If you share design specifications or procurement data with a subcontractor, and that subcontractor doesn't have adequate controls, that's a gap in your CMMC compliance posture, not theirs alone. The flow-down obligation means your assessment scope includes your supply chain data sharing practices.
Second, endpoints outside the managed environment. Remote workers, contractors using personal devices, and authorized users who save files locally all represent CUI boundary violations if those endpoints aren't within the SSP scope and protected accordingly.
Third, the collaboration platform residue. When a project closes, CUI shared via Teams channels, Slack workspaces, or SharePoint sites frequently remains accessible to users whose project access should have been revoked. Persistent access after authorization ends is a finding under access control practices 3.1.1 and 3.1.2.
Self-Assessment vs. C3PAO: The SPRS Score and Legal Risk
CMMC Phase 1 began in November 2025.
Phase 2 — when DoD can condition contract awards on Level 2 C3PAO third-party assessments — begins November 2026.
Until then, Level 2 compliance is demonstrated through self-assessment and SPRS submission.
The SPRS score is not just a compliance metric; it’s a legal representation of the federal government. A self-assessment that overstates compliance, knowingly or through negligence, creates False Claims Act exposure. FCA penalties include civil penalties of $13,000+ per claim plus treble damages. Several defense contractors have faced FCA enforcement for inaccurate SPRS submissions.
The POA&M (Plan of Action and Milestones) provides a remediation window for identified gaps — typically 180 days — but it does not protect against FCA claims if the underlying assessment was not conducted in good faith. Conduct your self-assessment against actual evidence, not assumed implementation.
Building the CMMC Evidence Package
A defensible CMMC assessment evidence package addresses every practice in scope with:
- Policy documentation — the written policy that mandates the control.
- Implementation evidence — configuration exports, system screenshots, and audit logs.
- Scope mapping — documentation of which systems, users, and data flows the control applies to.
- Testing results — evidence that the control was tested and operates as described.
For practices with technical controls (encryption, MFA, logging), the evidence should include tool-specific configuration exports, not narrative descriptions. The assessor will ask to see the configuration. "We use MFA" is not evidence.
A screenshot of the Entra ID conditional access policy, an export of the device compliance policy, and a sample of the MFA enforcement logs — that's evidence.
CMMC: 30-Day C3PAO Pre-Assessment Readiness Checklist
Use this checklist to identify documentation and evidence gaps specifically mapped to CMMC Level 2 practice areas before your formal C3PAO assessment begins. Each item maps to a commonly deficient practice area.
| Readiness Item | Full Governance | Compliance Gap |
|---|---|---|
| SSP documents all systems that process, store, or transmit CUI — including endpoints, cloud services, and collaboration tools | Complete ☐ | Gap ☐ |
| FIPS 140-3 validated encryption deployed for CUI at rest and in transit — with CMVP certificate number documented | Complete ☐ | Gap ☐ |
| MFA enforced on all CUI-accessible accounts — including service accounts and shared accounts | Complete ☐ | Gap ☐ |
| Audit logs capture required events (3.3.1 / 3.3.2) — log retention policy matches requirements | Complete ☐ | Gap ☐ |
| User access reviews documented — terminated users and changed roles reflected within the required timeframe | Complete ☐ | Gap ☐ |
| Subcontractor data sharing — flow-down requirements documented and subcontractor security posture assessed | Complete ☐ | Gap ☐ |
| Incident response plan — tested within the last 12 months, with evidence | Complete ☐ | Gap ☐ |
| Configuration management baseline — documented and reviewed for all in-scope systems | Complete ☐ | Gap ☐ |
| POA&M — all identified gaps documented with realistic remediation timelines | Complete ☐ | Gap ☐ |
| Evidence package — implementation evidence exists for each practice, not just policy statements | Complete ☐ | Gap ☐ |
How Theodosian Addresses CMMC Level 2 Evidence Requirements
Theodosian satisfies 20+ CMMC Level 2 practices across the AC (Access Control), SC (System and Communications Protection), AU (Audit and Accountability), and IR (Incident Response) domains. For the specific gap areas that most often produce assessment failures:
Per-file FIPS 140-3 validated encryption closes practice 3.13.10 with a documented, certificate-bearing encryption module. Every CUI file is encrypted at the file level, not at the server level, which means the encryption follows the file whether it's on a managed endpoint, shared with a subcontractor, or accessed remotely.
Cryptographically timestamped access logs provide the audit evidence required under 3.3.1 and 3.3.2 — who accessed which file, when, from which device, and under what policy conditions. The evidence package maps directly to practice requirements.
Instant revocation provides the ability to terminate access to any file or user instantly across all sessions and devices, addressing the persistent-access-after-authorization gap that assessors consistently flag.
Identify Your Assessment Gaps Before the C3PAO Does
The November 2026 deadline for C3PAO assessment conditioning is approaching. Defense contractors who identify documentation and evidence gaps now have time to remediate. Contractors who discover them during an assessment don't.
🔒 Is Your CUI Handling a Liability or an Asset?
With Phase 2 arriving in November 2026, "doing security" isn't enough; you have to prove it. Close the gaps and secure your supply chain flow-down in minutes, not months.
FAQs: Closing the Gaps on CMMC Level 2
What's the difference between a CMMC Level 2 self-assessment and a C3PAO assessment?
A self-assessment is conducted by the organization itself and submitted to the SPRS system as a legal representation of compliance. A C3PAO assessment is conducted by an accredited third-party assessment organization, required for contracts involving sensitive CUI where DoD determines higher assurance is needed. Phase 2 begins in November 2026, when DoD can condition contract awards on C3PAO assessments. Self-assessment scores submitted without supporting evidence create False Claims Act exposure.
Which CMMC Level 2 practices are most commonly cited as deficient?
The most frequently deficient practices in pre-assessment reviews are: 3.13.10 (FIPS-validated encryption — organizations use encryption but not FIPS 140-3 validated modules), 3.3.1 and 3.3.2 (audit logging — events not captured or log retention insufficient), 3.1.1 and 3.1.2 (access control — persistent access after role changes or terminations), and 3.11.2 (vulnerability scanning — not conducted at required frequency with evidence).
What is a POA&M, and how does it affect CMMC assessment scores?
A Plan of Action and Milestones document identifies gaps and the timeline for remediating them. Under CMMC, a POA&M is permitted for certain practices, which allows an organization to proceed with an assessment while documenting a remediation path. However, POA&M items still reduce the SPRS score, and practices scored as "not implemented" without a POA&M receive a zero. The minimum passing SPRS score for CMMC Level 2 is 80% (88 out of 110 points). A POA&M provides a 180-day remediation window, not a permanent pass.
Does per-file encryption satisfy CMMC Level 2 encryption requirements?
Yes. When the encryption module is FIPS 140-3 validated. NIST SP 800-171 control 3.13.10 requires FIPS-validated cryptography, which specifies validated modules listed in the NIST CMVP database. Theodosian's per-file encryption uses FIPS 140-3 validated modules. The SSP must document the specific module, its CMVP certificate number, and deployment scope to satisfy the evidence requirement under 3.13.10.
How does subcontractor data sharing affect our CMMC assessment scope?
Any system, person, or process that handles CUI falls within the CMMC scope, including how you share CUI with Tier 3 subcontractors. If CUI flows downstream to a subcontractor without adequate controls, that is a finding against your compliance posture. DFARS clause 252.204-7012 requires flow-down of security requirements to subcontractors who handle CUI on your behalf. Your SSP should document subcontractor data sharing practices and evidence that flow-down obligations are met.
