Nearly every CMMC implementation guide on the internet gives you the same answer: 12 to 18 months. Start early. Don't wait. The deadline is November 2026.
While that timeline is a reality for traditional infrastructure overhauls, it doesn't account for modern, API-driven remediation. This isn't about how long the whole list takes, but how to sequence your implementation so that the controls C3PAO assessors scrutinize most—the encryption and key management domain—are closed first, not last.
The 12-to-18-month estimate is an average across all 110 NIST 800-171 controls. Some of those are policy documents you can produce in a day; others are configuration changes that take an afternoon. However, in a legacy environment, the cryptographic and media protection controls can take months to architect and deploy. With a file-centric approach, those same controls are closed in weeks. If your plan treats every control with the same 18-month urgency, you're wasting time on paperwork while your biggest technical gaps remain wide open.
Here's the honest, accelerated timeline, broken down by what the file security domain actually requires.
Why File Security Controls Delay Assessments
The controls that most often produce "NOT MET" findings in C3PAO assessments aren't the access management controls or the configuration management controls. They're the ones where the gap between what the SSP says and what the environment actually does is widest.
File security controls — SC.3.177 (FIPS-validated encryption), SC.3.187 (key management), and MP.2.121 (media protection on contractor devices) — are the three most frequently cited gaps for the following reason: organizations inherit a false sense of coverage from tools they already have.
BitLocker satisfies part of SC.3.177. Microsoft Purview satisfies part of the access control posture. An MDM solution satisfies part of MP.2.121. But "partial" is not "MET" in a C3PAO assessment. Assessors score each practice as fully met or not. If your CUI protection is conditional on the device being managed, or conditional on the file staying inside your Microsoft tenant, or conditional on your subcontractors using the right email client, that conditionality is exactly what a skilled assessor probes for.
The organizations that sail through assessments aren't the ones with the most tools. They're the ones who closed the gap between their SSP claims and their actual environment, in the file security domain first.
The File Security Implementation Phases
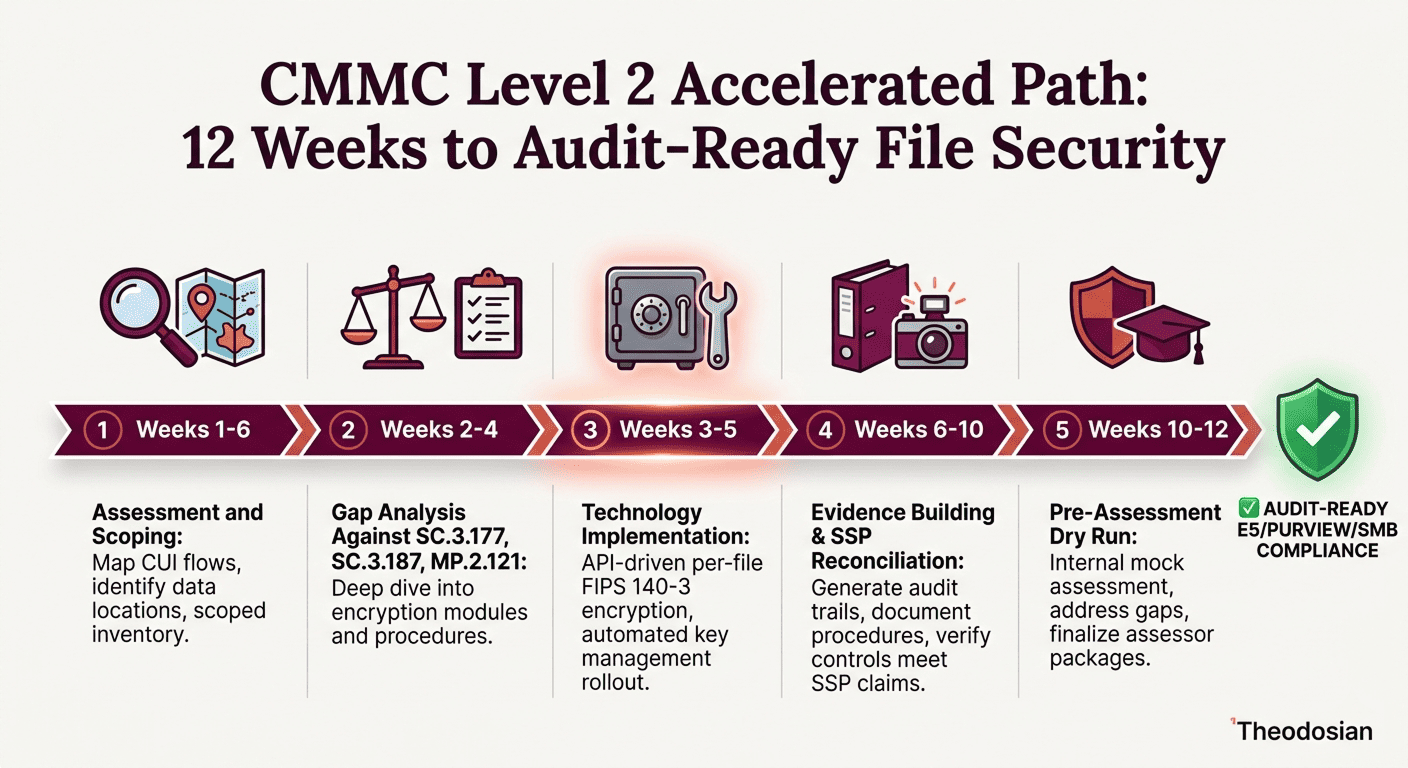
Phase 1: Assessment and Scoping (Weeks 1–6)
Before you can implement file security controls, you need to know exactly where your CUI lives. This is consistently the most underestimated phase — not because it's technically complex, but because the answer is almost always more uncomfortable than expected.
What this involves: Mapping every system, device, and location that stores, processes, or transmits CUI. This includes managed endpoints, shared drives, email, cloud storage, removable media, and the devices of any subcontractors who touch CUI in your supply chain.
What most organizations discover: CUI is in more places than the SSP currently reflects. It's on personal devices that weren't in scope. It's in email threads that aren't classified. It's in a Dropbox folder that a contractor set up three years ago because the network share was slow.
Output required: A scoped CUI inventory that matches what you'll tell the assessor. The SSP has to reflect reality, not what you wish reality were. The False Claims Act risk isn't just theoretical here: contractors who self-attested to compliant SSPs that didn't reflect their actual security posture have faced DOJ action. That risk doesn't evaporate in Phase 2 — it compounds, because now there's a third-party assessor involved.
Phase 2: Gap Analysis Against SC.3.177, SC.3.187, and MP.2.121 (Weeks 2–4)
While scoping continues, begin the control-specific gap analysis. These three controls should be prioritized first:
SC.3.177 — Employ cryptographic mechanisms to protect the confidentiality of CUI during transmission and at rest: The specific requirement is FIPS-validated cryptographic modules — not FIPS-approved algorithms. The distinction matters: an algorithm can be FIPS-approved but implemented in a module that hasn't undergone CMVP validation. Assessors are trained to check the CMVP validation certificate, not just the algorithm name. If your encryption tool's validation certificate has lapsed or was never obtained, you'll fail this control regardless of the algorithm used.
SC.3.187 — Establish and manage cryptographic keys for required cryptography employed in organizational systems: Key management is consistently underestimated. This control requires documented processes for key generation, distribution, storage, access, rotation, and destruction. "Keys are managed by Microsoft" or "keys are managed by the cloud provider" is not a sufficient answer — the assessor will want to see your documented key management procedures and evidence that they're followed.
MP.2.121 — Protect system media containing CUI, both paper and digital: For digital media, this means CUI on any media — managed laptops, removable drives, and contractor-controlled devices — is protected. BitLocker on managed endpoints addresses part of this. But if subcontractors handle CUI on personal devices that aren't managed by your MDM, this control has a gap. The solution that closes it is protection that follows the file rather than the device.
Output required: A written gap assessment for each of the three controls, with current state, target state, and a sequenced remediation plan.
📋 Know What the Assessor Will Ask Before They Ask It
The CMMC Assessment Readiness Checklist maps every evidence requirement for SC.3.177, SC.3.187, and MP.2.121 — with specific documentation requirements and audit trail examples.
Phase 3: Technology Implementation (Weeks 3–5)
This is where the clock gets real. Technology implementation for legacy file security typically takes 8 to 12 weeks. However, by using Theodosian’s per-file encryption, this phase can be compressed into 2 to 3 weeks. Because there is no data migration or workflow disruption, EAR and CUI controls can be active almost immediately, allowing you to spend those extra weeks on evidence building rather than troubleshooting.
For small to mid-size defense subcontractors (50–500 users), the implementation sequence typically looks like:
Week 3: Deploy per-file encryption for CUI documents. This should cover all file types that carry CUI — not just PDFs and Word documents, but CAD files, spreadsheets, schematics, and any other format used in your contracts. Configure access policies that enforce least privilege: identity, role, device trust status, location, and time-based controls. A well-configured per-file encryption deployment means that if a file ends up where it shouldn't, the unauthorized process gets nothing — access is denied unless contextual controls are met.
Weeks 3–4: Document and Enforce Key Management. This is where the administrative work catches up with the technical work. Your key management documentation must match your deployed architecture. If you've deployed a zero-knowledge, decentralized key management system, your SSP procedures section must describe exactly that — not a generic "we use cloud-managed keys" statement.
Weeks 4–5: Close the MP.2.121 gap. This typically requires either enrolling subcontractor devices in your MDM (often impractical) or deploying a file-level encryption approach that protects CUI on devices outside your managed fleet. File-level encryption that follows the document — rather than depending on the device — is the practical solution here.
Note on timelines: Organizations with ISO 27001 or SOC 2 frameworks already in place typically shorten this phase because foundational access management and key management procedures are already documented.
Phase 4: Evidence Building and SSP Reconciliation (Weeks 6–10)
The technology works. Now you have to prove it to a third party, who will score each control as MET or NOT MET.
Assessors evaluate three types of evidence: documentation (your SSP, key management policies, procedures), examination (system configurations, technical screenshots, logs), and interviews (your team describing what they do and how).
The SSP reconciliation step is critical and frequently rushed. Once your implementation is complete, go through every claim in your SSP file security section and verify it against your actual deployed environment. The gap between an SSP written during planning and the system that actually got deployed six months later is one of the most common sources of assessment failures.
Evidence package for SC.3.177: CMVP certificate for your encryption module, encryption configuration documentation, sample encrypted file evidence, and access control policy documentation.
Evidence package for SC.3.187: Key management policy document, key management procedures (generation, rotation, destruction), key custodian designations, and evidence of active key management practices.
Evidence package for MP.2.121: Device inventory showing all devices that access CUI, encryption status evidence for each device category, and specific coverage documentation for contractor-controlled devices.
Phase 5: Pre-Assessment Dry Run (Weeks 10–12)
Book a mock assessment with a CMMC Registered Practitioner Organization (RPO) before you bring in the C3PAO. A dry run surfaces the gaps your team has normalized. Assessors find things internal teams miss because familiarity creates blind spots.
Budget 8 to 12 weeks' lead time when booking your C3PAO assessment. The assessor supply problem is real: as of Q1 2026, C3PAOs are reporting booking backlogs of 10 to 16 weeks. Organizations that wait until October 2026 to schedule an assessment will find they can't get one before the November deadline.
The Honest Bottom Line
If you're starting from scratch today — April 2026 — you have approximately 28 weeks until the November 10 Phase 2 deadline, which is more than double the time needed to fully remediate file security with Theodosian. That's tight but achievable if file security controls are prioritized immediately and the scoping phase doesn't drag.
If you already have managed endpoint encryption in place, the primary remaining risk is the CUI that moves beyond your managed environment. If you are closing the file-layer gap with Theodosian, the implementation itself is measured in days, not months. This allows you to move directly into Phase 4 (Evidence Building) by Month 1, significantly de-risking your November 2026 deadline.
The organizations that miss the deadline are the ones that treated the timeline as a planning exercise rather than an implementation schedule, and discovered in August that their encryption controls weren't as complete as their SSP suggested.
A note on cost: The DoD estimates the average three-year compliance cost for small defense contractors at approximately $487,970. The organizations getting to the bottom of that range — not the top — are the ones who front-loaded the file security layer early, avoided costly remediation after a failed assessment, and didn't spend months engineering a BitLocker + MDM + policy exception workaround for a problem that per-file encryption solves directly.
🔒 Close the File Security Gap Before the Assessor Finds It
The 14-day pilot demonstrates full file-level FIPS 140-3 encryption, key management, and assessor-ready evidence generation in your environment.
FAQs: CMMC Level 2 Timeline & Implementation
How long does CMMC Level 2 certification actually take, and why does it vary so much?
The 12-to-18-month figure is a legacy average based on "bottom-up" infrastructure rebuilds. In 2026, the timeline is determined by your remediation strategy. While policy documentation still takes time, the "Technology Implementation" phase—historically the 3-to-6 month bottleneck—can now be compressed to under 3 weeks. Organizations starting today (April 2026) can achieve audit-readiness by July, provided they prioritize the high-failure encryption controls (SC.3.177, SC.3.187) in their first 30 days.
What is the difference between a CMMC RPO and a C3PAO, and which do I need?
An RPO (Registered Practitioner Organization) helps you build the plane; a C3PAO (Certified Third-Party Assessment Organization) inspects it. For a Level 2 mandate, a C3PAO is required for your triennial certification. Note for 2026: As we approach the November 10 Phase 2 deadline, C3PAO backlogs have stretched to 16+ weeks. By using an accelerated 12-week implementation path, you can engage a C3PAO months earlier than competitors who are still stuck in legacy remediation, effectively "cutting the line" for your audit slot.
Can I self-attest for CMMC Level 2, or is a C3PAO assessment mandatory?
CMMC Level 2 is split into two tracks. Some contracts will allow annual self-attestation by a senior company official (signed via the Supplier Performance Risk System). Others — specifically those involving CUI designated as higher-priority by the DoD — will require a triennial C3PAO third-party assessment. The specific requirements for your contracts will be specified in your RFPs and contract clauses (DFARS 252.204-7021). If you handle any CUI that falls under the mandated C3PAO track, self-attestation is not an option. When in doubt, assume C3PAO will be required — the documentation and evidence preparation are identical regardless of the assessment pathway.
What happens if a defense contractor misses the November 2026 CMMC Phase 2 deadline?
Contracts awarded after November 10, 2026, that require CMMC Level 2 certification will include DFARS clause 252.204-7021. Without the required certification in place, a contractor cannot be awarded those contracts. For existing multi-year contracts, the CMMC requirement typically applies at renewal or option exercise. Beyond contract eligibility, there's a False Claims Act dimension: contractors who self-attest to CMMC compliance that they don't actually have face DOJ liability. A missed deadline isn't just a competitive disadvantage — it's a potential legal exposure.
Which CMMC Level 2 controls are the hardest to close, and why should I prioritize them?
SC.3.177 (FIPS-validated encryption) and SC.3.187 (Key Management) are the top "assessment killers." They are hard because most tools only protect the container (the laptop or the cloud tenant), not the content (the file). We advocate for a "File-First" priority because these controls are the most scrutinized by assessors. By closing these gaps in Week 3 of your journey rather than Month 10, you create a "Compliance Anchor" that makes the rest of your 110-control audit significantly smoother.
