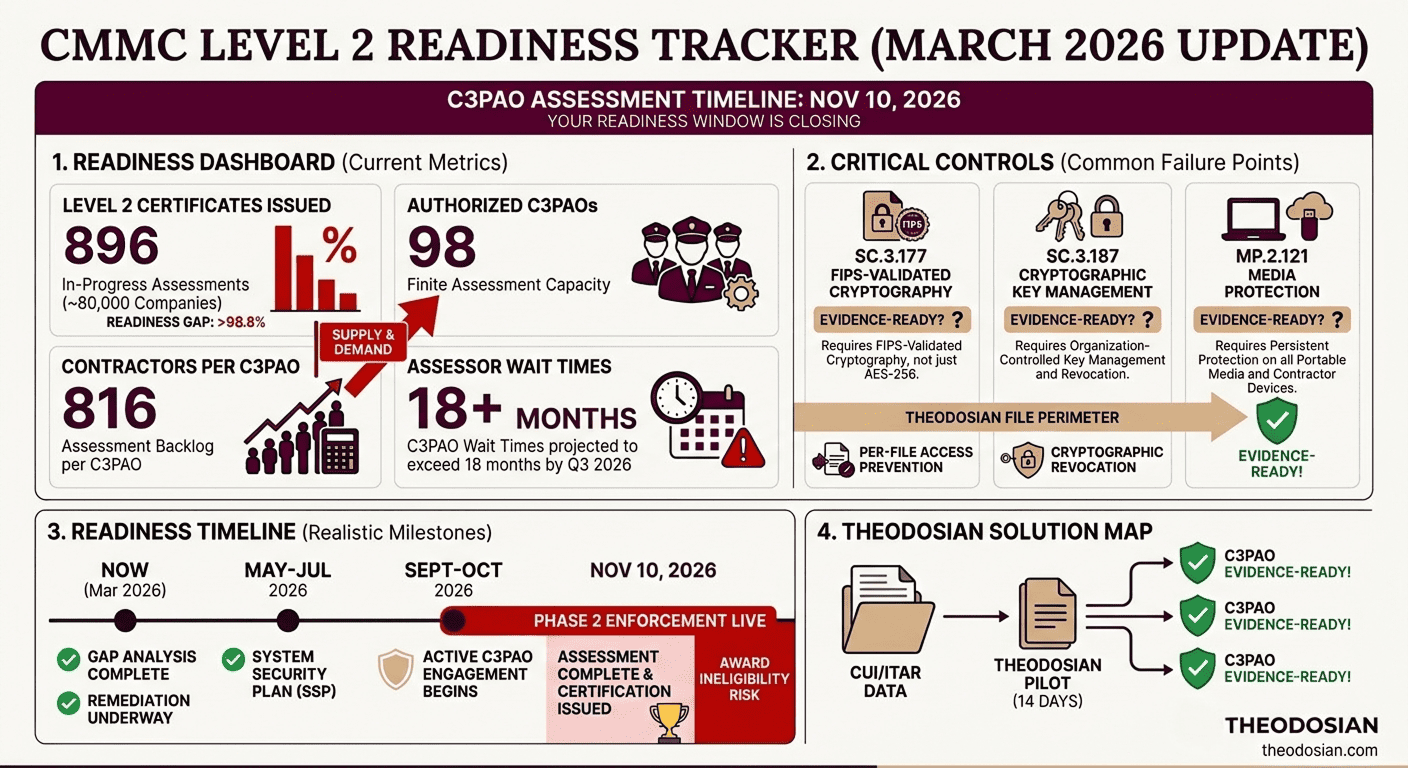
While the assessor pool is growing, the supply remains critically low. With only 765 CCAs authorized to lead assessments. There are approximately 80,000 defense contractors that will need CMMC Level 2 certification. Phase 2: When C3PAO third-party assessments become mandatory for most of those contractors, it locks in on November 10, 2026.
The math is already broken. Wait times for new C3PAO clients are projected to exceed 18 months by Q3 2026. Contractors who haven't started the assessment pipeline by now are not running late. They are at risk of missing the window entirely, regardless of how mature their controls are.
This is the CMMC story most compliance guides skip: the deadline isn't only about readiness, it's about queue availability. And the queue is filling faster than the assessor pool is growing.
📋 Already Assessing Your CMMC Gaps?
See how Theodosian maps directly to CMMC Level 2 encryption and media protection controls, without displacing your existing infrastructure.
What Changes On November 10, 2026, for CMMC
Phase 1 of CMMC enforcement began on November 10, 2025. From that date, DoD began incorporating CMMC requirements into applicable solicitations via the revised DFARS clause 252.204-7021. Phase 1 is predominantly self-assessment: contractors handling CUI on non-prioritized contracts, submitting their scores to SPRS, and signing annual affirmations.
Phase 2, beginning November 10, 2026, ends the self-attestation era for the majority of Level 2 contractors. Third-party C3PAO assessments become mandatory for contracts involving CUI on prioritized acquisitions, which includes the bulk of defense program work. Self-assessment will remain available only for a narrow subset of non-prioritized contracts.
What this means operationally:
- An active C3PAO engagement must be in your timeline before Phase 2 contracts can be awarded or renewed.
- "Conditional Level 2" certifications (issued when a contractor passes the assessment with an accepted Plan of Action and Milestones) carry a 180-day remediation window, not a permanent workaround.
- Contractors whose contracts renew post-November 10, 2026, without a C3PAO assessment on record face potential award ineligibility.
The Phase 2 trigger isn't a future event to plan around. For any contractor whose DoD contract renewal falls in 2026, the assessment needs to be underway now.
Why Is There an Assessor Supply Problem for CMMC Accreditation?
The CMMC Accreditation Body (The Cyber AB) oversees C3PAO authorization. As of early 2026, approximately 80–100 authorized C3PAOs are operational; each with finite assessment capacity and a growing forward book.
Industry estimates put the assessor capacity needed to process 80,000 Level 2 certifications at between 2,000 and 3,000 Certified CMMC Assessors. Current supply is under 800. The gap isn't closing fast enough to prevent a bottleneck at scale.
In practice, this means:
- C3PAOs operating in high-demand regions (defense corridor states, aerospace hubs) are already scheduling into late 2026 and 2027.
- Contractors with complex environments, such as multi-site operations, large subcontractor networks, and significant CUI repositories, require longer assessment engagements and are booking earlier.
- Gap analysis and remediation work, which typically precede the formal assessment, add 6–12 months to the total timeline.
A contractor starting their gap analysis in Q2 2026 is already outside the realistic window for Phase 2 compliance before contract renewal pressure hits.
What Evidence-Driven Assessment Actually Looks Like
Self-attestation required a score in SPRS and a signed affirmation. C3PAO assessment requires evidence, specific, artifact-based proof that each of the 110 NIST SP 800-171 controls is implemented and functioning.
For the encryption control family, assessors will not accept policy documentation alone. They will ask to see:
- The NIST CMVP certificate number for cryptographic modules in use.
- A live demonstration of access controls on CUI that has left the organizational perimeter.
- Key management documentation — how keys are generated, rotated, protected, and what happens to access when a contractor is offboarded.
That last point is where most assessments stall. "We removed their SharePoint access" is not an acceptable answer to the question of how CUI on a former contractor's device is protected. The assessor is asking about the file, not the folder. SC.3.177 requires FIPS-validated encryption that travels with the data. MP.2.121 requires that protection to persist on portable and contractor-managed media.
What Controls Are Most Contractors Currently Failing On?
Encryption is consistently among the highest-failure control families in CMMC Level 2 assessments. Three controls carry the most weight:
SC.3.177 — FIPS-Validated Cryptography: The requirement is not AES-256. It is a cryptographic module validated under the NIST Cryptographic Module Validation Program (CMVP). Standard commercial platforms — SharePoint, Teams, standard cloud storage — apply platform-level encryption to their own infrastructure. They do not apply FIPS-validated encryption at the individual file level. CUI downloaded to a contractor's device is unprotected the moment it leaves the managed environment.
SC.3.187 — Cryptographic Key Management: Key management must be within the organization's control — not the cloud provider's. If your storage platform holds the encryption keys, you cannot demonstrate granular key management, cannot show evidence of per-contractor access controls, and cannot demonstrate what happens to key access when personnel change. The assessor will ask.
MP.2.121 — Media Protection: CUI on removable media, contractor laptops, and personal cloud storage must maintain the same protections as CUI on organizational systems. This is the control that catches the most contractors off guard — because it applies to files that were legitimately downloaded by authorized users, not just exfiltrated data.
The common thread across all three: they require protection that travels with the file, not protection that stops at the server boundary. Per-file FIPS 140-3 validated encryption with contextual access controls — evaluated on every open attempt against identity, device, location, network, and time parameters — is the architecture that satisfies all three simultaneously.
A Realistic C3PAO Assessment Readiness Timeline
Working backwards from November 10, 2026:
| Milestone | Realistic Deadline |
|---|---|
| C3PAO assessment complete | September 2026 (latest) |
| Active C3PAO engagement begins | March–April 2026 |
| Remediation of identified gaps | Now through Q1 2026 |
| Formal gap analysis complete | Already overdue for many |
| System Security Plan (SSP) documented | Should already exist |
Contractors who completed Phase 1 self-assessments with honest scores will have documented gap inventories. The honest scores matter: SPRS submissions are subject to DoJ False Claims Act exposure, and C3PAOs will assess against actual implementation, not documented intent.
The remediation window is not 2026; it is now. Contractors treating Phase 2 as a 2026 problem are already behind the timeline needed to secure an assessment slot before contract renewal pressure forces the issue.
Generating CMMC Assessment Artifacts: What You Can Control Before The Auditor Arrives
C3PAO readiness is not just a compliance exercise; it’s an evidence-packaging exercise. The controls that generate passing evidence for SC.3.177, SC.3.187, and MP.2.121 are the same controls that close the structural security gaps most contractors have in their CUI handling workflows.
Specific actions that produce verifiable assessment evidence:
File-Level Encryption Implementation: Replace platform-level permission management with FIPS 140-3 validated per-file encryption. Each file carries its own encryption and access policy. When a contractor's access context is no longer valid — wrong device, expired authorization, offboarding — the next open attempt is denied by the contextual check. No file retrieval required. No chasing CUI across contractor devices.
Contractor Access Audit Trail: The assessor will want a record of who had access to which CUI, for how long, and what happened to that access at offboarding. Per-file contextual access controls generate this automatically. A permission log in SharePoint does not — it shows who had folder access, not file-level governance history.
Offboarding Controls Documentation: MP.2.121 requires demonstrable offboarding controls for CUI on contractor media. The question isn't "did you remove their system access?" — it's "can you demonstrate that CUI on their devices is no longer accessible?" Contextual access policies answer that question at the file layer. System access removal does not.
Is Your Team Ready for the November Deadline? The 90-Day CMMC Prioritization Checklist
If you are aiming for a late-2026 C3PAO assessment, your "remediation" window is closing. Prioritize these high-impact tasks to ensure your evidence is ready before the assessor arrives.
- [ ] Audit Your "Removable Media" Workflow (MP.2.121): Can you prove that CUI on a contractor’s laptop is cryptographically "killed" the moment they are offboarded? If your answer is "we trust them to delete it," you have a critical failure point.
- [ ] Validate Your FIPS Modules (SC.3.177): Don't just check for "AES-256." Locate the NIST CMVP certificate number for every encryption tool you use. Assessors will ask for this specific number to prove FIPS 140-3 validation.
- [ ] Formalize Key Ownership (SC.3.187): If your cloud storage provider holds your encryption keys, you do not have "independent control." Move toward a "Bring Your Own Key" (BYOK) or customer-managed key architecture.
- [ ] Map CUI Flow (Not Just Storage): Draw a map of where CUI goes after it's downloaded. If CUI touches an unmanaged device (contractor/personal), ensure the file itself carries the protection, not just the folder.
- [ ] Lock Your C3PAO Slot: If you are at a "70 or higher" SPRS score, start interviewing C3PAOs now. Waiting for a "perfect 110" to book your slot will likely land you in a 2027 queue.
📋 Get The Full CMMC Compliance Checklist
The 5-point sprint above covers your 90-day priorities. This full checklist maps all 25 actions across the complete 12–18 month readiness journey — from SSP documentation to evidence packaging to locking your C3PAO slot.
FAQ: CMMC 2.0 And The November 2026 Deadline
Is self-attestation going away entirely after CMMC Phase 2?
Not entirely. Self-assessment remains available for a narrow category of non-prioritized contracts that the DoD designates as not requiring C3PAO certification. However, the majority of contracts involving CUI — particularly those tied to defense programs, ITAR-controlled technical data, or sensitive program information — will require C3PAO assessment under Phase 2. Contractors should not assume their contract falls in the self-assessment category without explicit confirmation in the solicitation language.
What is a Conditional Level 2 certification, and is it acceptable for a contract award?
A Conditional Level 2 certification is issued when a contractor passes the C3PAO assessment but has an accepted Plan of Action and Milestones (POA&M) for controls not yet fully implemented. It is not a permanent certification — the POA&M has a 180-day remediation deadline. Whether a Conditional Level 2 is acceptable for contract award depends on the specific contracting officer and solicitation requirements. It should not be treated as a reliable fallback position for Phase 2 compliance.
How long does a C3PAO assessment actually take?
Assessment duration varies by organization size and environmental complexity. For a mid-sized defense subcontractor, a C3PAO assessment typically takes 4–8 weeks of active assessment work — not including the pre-assessment preparation, documentation review, and any remediation that precedes the formal engagement. Total time from gap analysis initiation to final certification: 12–18 months for most organizations starting from a moderate baseline.
Which contracts will require CMMC Phase 2 certification?
Phase 2 requirements will appear in solicitations that the DoD designates as requiring CMMC Level 2 — primarily contracts involving the handling, processing, or storage of CUI. This includes most prime contracts and flows down to subcontractors who handle CUI as part of program delivery. The specific CMMC level required will be identified in the solicitation's DFARS 252.204-7021 clause.
What happens if a contractor misses the November 2026 C3PAO assessment deadline?
Contractors without a required CMMC certification on record will be ineligible for award on contracts that specify CMMC as a requirement. For contracts already in performance, contracting officers have discretion — but DoD has been clear that CMMC compliance is a contract eligibility condition, not a reporting requirement. Missing the Phase 2 window while holding active contracts with CUI handling obligations creates both award risk and potential False Claims Act exposure for ongoing self-attestation.
