Your spreadsheet has six vendors. Your budget has one line item. Your board expects clarity. Your CISO knows the reality: enterprise data protection software has fragmented into five categories, each solving a different problem, and buying the wrong one, or worse, a misaligned combination, leaves you exposed.
This guide cuts through the noise.
We'll examine the five categories of data protection that matter in 2026, review the market leaders in each, add one specialist tool that occupies its own sub-category, and expose the one critical gap that most major platforms share. Then we'll show you how to think about building a stack that actually holds up under a compliance audit or a breach investigation.
Why Data Protection Matters Now
The perimeter is dead. The supply chain is fractured. Your data lives on contractor devices, in cloud tenants you don't fully control, and on personal endpoints your IT team never sees. Meanwhile, CMMC, ITAR, and state privacy laws keep tightening the definition of what "protected" means.
The old answer—"buy a DLP, bolt on a backup solution, hope it works"—no longer closes the gap. In 2025, 66% of breach victims said they discovered the breach because a third party told them. Not because their tools caught it. Not because their controls held. Because someone else noticed.
If you're responsible for data security at a defense contractor, regulated manufacturer, or any organization handling sensitive intellectual property or compliance-critical data, you need to understand what each category actually protects, and what it doesn't.
The Five Categories of Data Protection (And What They Actually Do)
1. Data Loss Prevention (DLP)
What it does: Monitors and controls the movement of sensitive data across networks and devices. It identifies sensitive information (credit cards, PII, trade secrets) and blocks or logs attempts to move it outside approved channels.
Real scope: Works on managed endpoints, email gateways, cloud integrations. Requires network visibility and agent deployment. Enforces policy at the moment of action, but only in environments you control and can monitor.
Blind spots: Offline devices, air-gapped networks, data already outside your perimeter. Works at policy enforcement time; doesn't protect the data object itself.
2. Data Security Posture Management (DSPM)
What it does: Discovers where sensitive data lives, who can access it, what permissions exist, and whether those permissions are actually justified. Behavioral analytics flag unusual access patterns.
Real scope: Maps unstructured data—files, databases, shares—and creates visibility into access history. Strong for detecting over-provisioned access and suspicious user behavior. Good for audit evidence.
Blind spots: Doesn't control access; identifies it. Doesn't encrypt the data; catalogs it. Reactive rather than preventive.
3. Backup and Disaster Recovery (BDR)
What it does: Maintains immutable, recoverable copies of your data. Protects against ransomware by offering an offline, unencrypted copy to restore from. Enables business continuity and RTO/RPO compliance.
Real scope: Essential for uptime guarantees and recovery from destructive incidents. Immutable snapshots prevent attackers from corrupting the primary backup. Strong compliance story for availability requirements.
Blind spots: Recovers data after it's compromised. Doesn't prevent exfiltration. Doesn't encrypt in-use or at-rest in your operational environment.
4. Endpoint Protection Platform (EPP) with Data Protection Features
What it does: Detects and blocks malware, ransomware, and suspicious behavior on endpoints. Modern EPPs include real-time file monitoring, behavioral threat detection, and in some cases, integration with data controls.
Real scope: Strongest when endpoint behavior is unusual or suspicious. Good for detecting execution-based attacks. Integration with cloud consoles allows policy enforcement across large fleets.
Blind spots: Assumes the endpoint is the threat surface. Doesn't protect data after it leaves the device. Assumes the endpoint's OS and agent remain trustworthy—a weak assumption for contractor or BYOD scenarios.
5. File-Level Encryption with Context-Aware Access Control
What it does: Encrypts individual documents with their own cryptographic keys and binds access control to the file itself. Access is denied at the decryption layer if identity, device, location, or time parameters aren't met, regardless of where the file is.
Real scope: Protection travels with the document. Works offline, on unmanaged devices, outside corporate networks. Access control applies everywhere the file goes. Creates an audit trail of every access attempt.
Blind spots: Requires a shift from network-perimeter thinking to data-object thinking. Requires key management infrastructure. Not a compliance checkbox, it's a foundational architectural choice.
🔒 Before Reviewing Vendors, Identify Your Own Hidden Vulnerabilities
See where your sensitive files are currently escaping your perimeter.
How We’ve Evaluated These Data Protection Platforms
We’ve assessed each platform against criteria that matter to CISOs at defense contractors and regulated enterprises:
- Coverage Scope: What data is actually protected? On which devices? In which environments?
- Compliance Alignment: Does it address CMMC Level 2 and 3 encryption controls? ITAR requirements? NIST 800-171?
- Managed vs Unmanaged: What happens when data leaves your corporate environment? Does protection remain?
- Real-Time Access Control: Can the system deny access at the moment of access, or only log it retroactively?
- Deployment Complexity: How long before this is truly enforced across your environment?
- Audit Trail Quality: If you're breached, what does the evidence package look like?
Data Protection Platform Reviews
Microsoft Purview
Category: Data Loss Prevention + Classification + Compliance Management
What it protects: Sensitivity labels, DLP rules, cloud app connectors, and endpoint DLP agent. Classification is comprehensive. Compliance templates for dozens of regulations. Baked into Office 365 and Windows 10/11.
Ideal org profile: Enterprises already deep in the Microsoft stack. Complex multi-cloud environment (Microsoft, Azure, some AWS/GCP integration). Sophisticated compliance and governance function.
Coverage boundary: Works best on managed endpoints with the DLP agent. Cloud app connectors require explicit integration. Data outside Microsoft's ecosystem or on unmanaged endpoints is difficult to control. Classification is accurate; enforcement is policy-based, not cryptographic. If someone copies a file to a personal cloud or a contractor's device, DLP rules don't travel with the data.
Strength: Enterprise breadth. If you live in Microsoft, this is comprehensive. Classification and labeling are strong.
Honest gap: Assumes managed environment and network visibility. Doesn't encrypt the data or control access at the file level. No protection for data on offline or contractor devices.
Varonis
Category: Data Security Posture Management (DSPM)
What it protects: Data discovery, classification, permissions analysis, user behavior analytics, threat detection. Strong visualization of access patterns and data risk.
Ideal org profile: Large enterprise with unstructured data sprawl. Complex Active Directory environments. Significant NAS and file server infrastructure. Teams that need visibility first, then control second.
Coverage boundary: Excellent for discovering what data you have and who can access it. Behavioral analytics flags unusual access. Doesn't encrypt data or control access cryptographically. Strong for audit evidence and investigation; reactive rather than preventive. Works on infrastructure you control; visibility degrades on shadow IT or contractor environments.
Strength: Best-in-class visibility into unstructured data. Behavioral threat detection is strong. Compliance reporting is solid.
Honest gap: Doesn't control access; identifies it. Doesn't protect data that moves. Assumes traditional IT infrastructure.
Rubrik
Category: Backup, Disaster Recovery, and Resilience
What it protects: Immutable snapshots, ransomware recovery, business continuity, data governance, and multi-cloud consistency. Strong isolation between backup and operational data.
Ideal org profile: Large enterprise with significant data volumes. Business continuity and RTO/RPO requirements are non-negotiable. Multi-cloud strategy (AWS, Azure, GCP).
Coverage boundary: Recovers data after compromise. Excellent for ransomware scenarios and availability. Immutable copies protect against encryption attacks. Doesn't prevent exfiltration. Doesn't control access on the operational copy. Strong post-incident; weak on pre-incident prevention.
Strength: Resilience architecture is proven. Immutable snapshots work. Recovery time is genuinely fast.
Honest gap: Backup protects you after the breach, not before. Doesn't protect data in use. Doesn't prevent attackers from stealing unencrypted operational copies.
CrowdStrike Falcon
Category: Endpoint Protection Platform (EPP) with Data Protection Features
What it protects: Malware and ransomware detection, endpoint threat hunting, behavioral threat detection, DLP agent integration, and in-cloud console. Real-time threat intelligence.
Ideal org profile: Endpoint-centric security team. Significant managed endpoint fleet. Need for rapid threat investigation and hunt capabilities. Teams already using CrowdStrike for AV/EDR.
Coverage boundary: Strong when the threat is active on the endpoint. Real-time detection is fast. Doesn't protect data after it leaves the endpoint (cloud, email, USB). Requires endpoint agent; unmanaged devices are invisible. Data protection layer is an add-on, not core.
Strength: Threat detection and incident response are fast. Endpoint telemetry is comprehensive.
Honest gap: Protects the endpoint, not the data. Data that moves to a personal cloud, email, or contractor device is unprotected. Doesn't enforce access control based on context.
Cohesity
Category: Enterprise Data Management + Backup + Governance
What it protects: Backup and recovery, data governance, ransomware protection, multi-cloud data consistency, and access control policies.
Ideal org profile: Large enterprise managing data across multiple clouds. Significant governance and compliance function. Need for unified backup architecture.
Coverage boundary: Similar to Rubrik in scope: strong on recovery and resilience. Governance features add visibility into what data exists and who accesses it. Doesn't encrypt individual files or control access at the file layer. Backup protects against destruction; it doesn't prevent exfiltration.
Strength: Unified data management across clouds. Governance and discovery features are strong.
Honest gap: Like other backup solutions, it protects post-incident, not pre-incident. Doesn't control access at the data object level.
Theodosian
Category: File-level encryption / data-centric security
Theodosian occupies a specific sub-category within data protection: per-file encryption. Unlike the other platforms in this list, Theodosian doesn't provide backup and recovery, data discovery, behavioral analytics, or endpoint protection. Its scope is narrower and more specific—applying FIPS 140-3 validated encryption to individual documents, with access governed by contextual controls that travel with the file.
The result is a form of data protection that functions outside managed environments. A document encrypted by Theodosian carries its own access policy regardless of device, network, or storage location. Identity, device trust status, geographic location, time, and role all factor into whether access is granted. If conditions aren't met, access is denied.
What it covers well: Organizations with data mobility challenges—where CUI or sensitive documents routinely move to contractor laptops, subcontractor networks, or external collaborators. Satisfies CMMC Level 2 controls SC.3.177 (FIPS-validated encryption), SC.3.187 (key management), and contributes to MP.2.121 (media protection on contractor devices). Zero-knowledge key architecture means encryption keys never leave the customer's control.
What it doesn't cover: Data discovery, backup, recovery, endpoint behavioral monitoring, or data classification. Most organizations deploying Theodosian have a separate DSPM or DLP tool for discovery and classification, and use Theodosian specifically for the protection layer on known-sensitive documents.
Ideal for: Defense contractors (CMMC/ITAR compliance), legal and professional services, and any enterprise where sensitive files travel beyond the managed device fleet.
Pricing: Free 14-day pilot. Enterprise pricing on request.
Data Protection Comparison Table
| Capability | Microsoft Purview | Varonis | Rubrik | CrowdStrike Falcon | Cohesity | Theodosian |
|---|---|---|---|---|---|---|
| Category | DLP + Classification | DSPM | BDR | EPP | Data Management | File-level encryption |
| Managed device coverage | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| Unmanaged/external device coverage | Limited (needs agent) | ❌ | ❌ | Limited (needs agent) | ❌ | ✅ (encryption travels with file) |
| Protection outside managed network | ❌ | ❌ | ❌ | ❌ | ❌ | ✅ |
| Real-time access denial | Policy-based | ❌ (detection only) | ❌ | Limited | ❌ | ✅ Contextual (identity, device, location, time) |
| File-level encryption | ❌ | ❌ | ❌ | ❌ | ❌ | ✅ |
| Context-aware access control | ❌ | ❌ | ❌ | Limited | ❌ | ✅ |
| CMMC/regulatory alignment | Partial | ❌ | Partial | Partial | Partial | ✅ SC.3.177, SC.3.187, MP.2.121 |
| Audit trail completeness | Good | Excellent | Good | Excellent | Good | ✅ Per-file access events |
| Backup/recovery | ❌ | ❌ | ✅ | ❌ | ✅ | ❌ Not in scope |
| Deployment time | 2-4 weeks | 4-8 weeks | 2-4 weeks | 1-2 weeks | 4-8 weeks | Days (integration with IdP) |
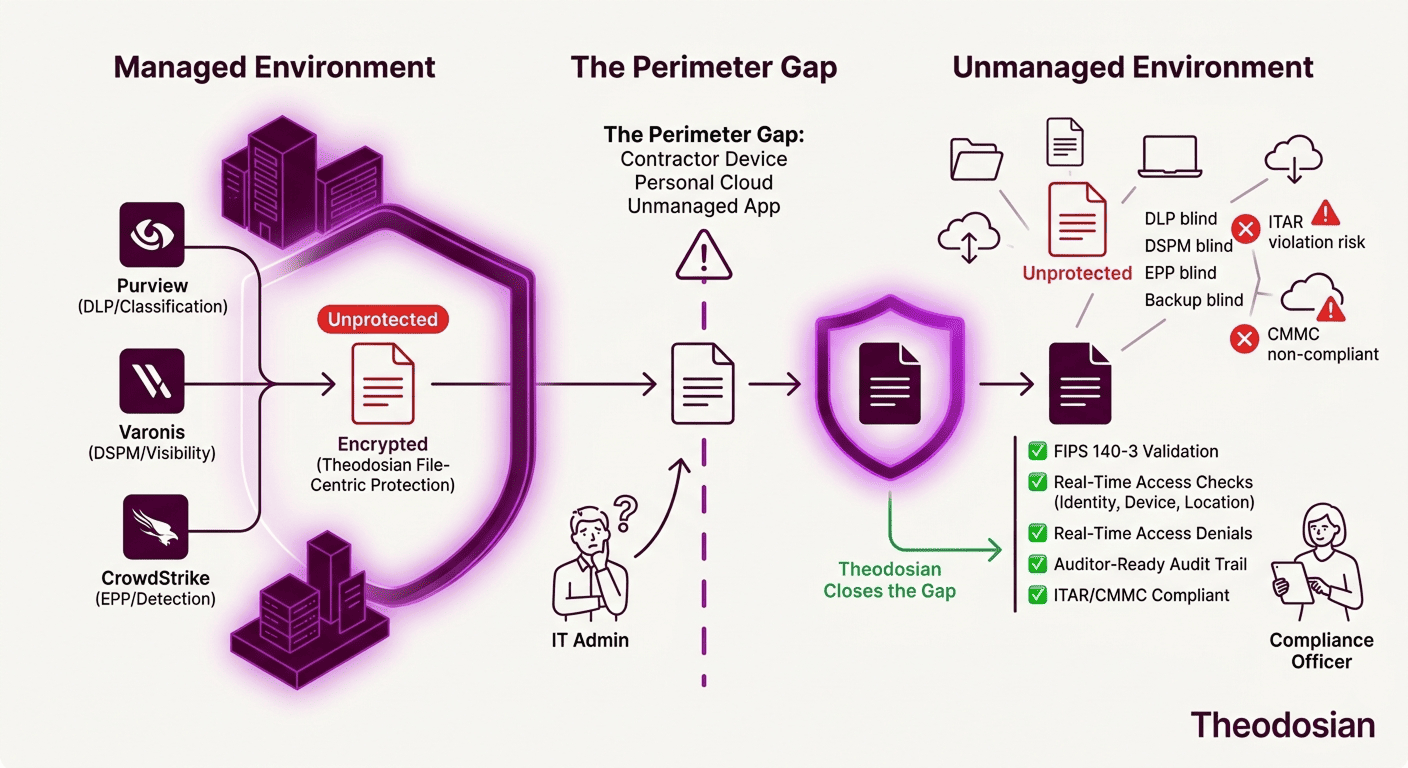
The Environment Gap That Data-Centric Security Closes
Look at that comparison table.
The critical distinction is "Unmanaged/External Device Coverage." Five of the six platforms assume you control the environment where data lives. They were built for enterprise data problems in enterprise environments: managed IT, known endpoints, corporate networks, and cloud tenants under your administration. For decades, that was the right model.
It is no longer sufficient.
A contractor receives a CAD file over email. He downloads it to his personal laptop. He opens it. He shares it with his team using his own Dropbox account. He takes it offline. Later, he emails it to a subcontractor on a different network, using a different email provider, on a different device.
At any point in that journey, your DLP doesn't see it. Your backup doesn't protect it. Your DSPM doesn't know it moved. Your EPP can't monitor the contractor's machine. Your endpoint doesn't exist in their environment.
Most data protection platforms assume: we know where the data is, and we control the network around it.
That assumption is broken.
The solution isn't to build better network controls. It's to protect the data itself. When a file carries encryption and contextual access control as properties of the document, not properties of the network, it remains protected regardless of where it goes. That's the architectural difference that file-level encryption represents in the data protection stack.
Why File-Level Encryption: The Specialist Tool in Your Stack
File-level encryption doesn't replace DLP, DSPM, backup, or endpoint protection. It complements them by solving a specific problem: protecting sensitive documents once they leave your perimeter.
Each document is encrypted with its own cryptographic key. The key is stored decentralized—not with the file, not in a centralized vault. Access is controlled by context: identity, device trust, location, time, and role. If the context requirements aren't met, access is denied at the decryption layer. Anywhere the file goes.
A CAD file encrypted with file-level encryption can be opened only if:
- The user's identity is verified (MFA, OAuth)
- The device meets your trust policy (endpoint detection, OS version, encryption status)
- The access attempt comes from an approved location or network
- The time is within approved business hours
- The user's role has permission to that document class
The contractor's personal laptop doesn't meet your device trust policy? The file won't decrypt. The subcontractor tries to open it at midnight on a weekend? Denied. Someone tries to copy the file to their personal cloud? The copy is useless without the context-bound key.
This is a specialist tool, not a replacement tool. Organizations deploying file-level encryption typically keep their DSPM (for discovery), DLP (for policy), and backup (for resilience), then add file-level encryption specifically for their crown jewels, the data sets that travel the most and carry the highest compliance risk.
Building Your Data Protection Stack
Not every organization needs file-level encryption. Not every data set requires it. The right stack depends on your threat model, your compliance requirements, and where your data actually lives.
For Defense Contractors (CMMC / ITAR)
Start with: Data discovery (Varonis or Purview) + File-level encryption for CUI (Theodosian) + Backup (Rubrik or Cohesity)
Why: Theodosian handles CUI and technical data. CMMC requires "encryption of classified information." The problem: CUI lives on contractor devices, personal cloud, and supply chain networks. File-level encryption ensures compliance no matter where the data goes. Discovery tells you what needs protection. Backup ensures you can recover if ransomware hits. DLP or EPP alone won't satisfy the auditor.
Evidence package for audit: File-level encryption logs prove controls were enforced. Device trust checks prove that only approved machines could decrypt. Backup proves you could recover if the original was compromised.
For Regulated Enterprises (Healthcare, Finance, Privacy Law)
Start with: DLP (Purview) + DSPM (Varonis) + File-level encryption for highest-sensitivity data (Theodosian) + Backup (Rubrik)
Why: You need visibility (DSPM), policy enforcement (DLP), and recovery (Backup). For your crown jewels—trade secrets, customer data, clinical trials—file-level encryption adds a control layer that doesn't depend on the network perimeter. The stack is deeper, but your audit evidence is airtight.
Evidence package for audit: Purview shows classification and policy. Varonis shows no over-provisioned access. File-level encryption shows encryption and access denial logs. Backup proves your recovery story.
For Hybrid Workforce / Contractor-Heavy Orgs
Start with: File-level encryption for sensitive documents (Theodosian) + Endpoint protection (CrowdStrike or equivalent) + DSPM for discovery
Why: Your data lives on personal devices and contractor networks. Endpoint tools can detect threats on managed machines. File-level encryption protects the data object itself, regardless of the device or network. This combination acknowledges that you can't control all endpoints, so you encrypt the data instead.
Evidence package for audit: File-level encryption logs show who accessed what, when, and from where. Device trust logs show that unmanaged devices couldn't decrypt. Endpoint tools show you're detecting threats on the machines you can see.
The Bottom Line
The best data protection software in 2026 isn't a single vendor. It's a combination: discovery (so you know what you have), policy enforcement (so you control movement), backup (so you can recover), threat detection (so you catch attacks), and—if your data leaves your perimeter—file-level encryption (so the data protects itself regardless of environment).
Five categories. Five leading platforms. One specialist tool. One foundational gap: data that has left your perimeter.
The platforms we reviewed are all strong in their categories. The question isn't which is "best." The question is which gaps in your current stack matter most to your threat model and your audit requirements.
If your data regularly leaves your perimeter—to contractors, to personal clouds, to supply chain networks—a specialist tool that provides file-level encryption isn't optional. It's foundational.
🔒 Start Protecting Data Where It Actually Lives
Most data protection stops at the perimeter. See how file-level encryption closes the gap for defense contractors and regulated enterprises.
FAQs: Data Protection Software
Can I just use DLP and call it data protection?
DLP is policy enforcement, not data protection. It works in networks you control and on endpoints where you've deployed the agent. The moment data moves to a contractor's device, personal cloud, or unmanaged endpoint, your DLP is blind. For compliance audits (CMMC, ITAR, NIST 800-171), auditors now ask: "What happens when CUI leaves your network?" DLP can't answer that. Encryption can.
Do I need file-level encryption if I already have endpoint protection?
Endpoint tools are threat-detection tools, not data-control tools. They're excellent at catching malware and ransomware. They don't prevent a legitimate user from copying a sensitive file to a personal cloud, and they can't protect data once it's on a device outside your visibility. File-level encryption handles the scenario endpoint tools weren't designed for: trusted users moving data to untrusted networks.
How does file-level encryption impact performance?
Unlike legacy tools that rely on caching to hide latency, Theodosian carries out contextual controls (identity, device trust, and location) in real-time for every single access request.
Because nothing is cached, your security posture is always current, denying access the millisecond a device becomes non-compliant. For standard enterprise workflows, this real-time check is measured in milliseconds and is imperceptible to the user. Audit trail logging is handled asynchronously to ensure that security enforcement never bottlenecks your productivity.
Is key management complex?
It depends on your architecture, but Theodosian simplifies the process without sacrificing control. We use a zero-knowledge, FILE_SEED-based model, which means your actual decryption keys are never in Theodosian’s possession.
- How it works: Instead of storing your keys, Theodosian manages a unique FILE_SEED for every protected document. This seed is a mandatory "ingredient" used to regenerate a file’s encryption key at the moment of access.
- The Governance: Your identity provider (Azure AD, Okta, or custom SAML) acts as the gatekeeper. Access to the file is only possible when your identity is verified and the FILE_SEED is provided.
- The CISO Perspective: This is significantly simpler than managing a centralized key vault. It removes the "honeypot" risk while providing Sovereign Continuity. Because we offer joint custody of your FILE_SEED lists, your enterprise maintains the ability to regenerate keys and access data independently, ensuring you are never "locked in" to a single vendor.
- The IT Ops Perspective: Implementation is straightforward; it leverages the identity infrastructure you already have in place to automate key lifecycle management at scale.
How do I know file-level encryption is actually working?
Theodosian provides audit logs for every access attempt (successful and failed), with full context: user, device, time, location, policy decision. If someone tries to open a file from an unapproved location or device, the log shows the denial. If you're running a CMMC or ITAR audit, these logs are your evidence package. You can pull real data to prove that encryption controls are enforced.
